The contemporary digital landscape demands a level of vigilance that transcends traditional perimeter defenses, especially as enterprise ecosystems become increasingly entangled with third-party vendors and opaque supply chains. While many organizations rely on point-in-time assessments to judge the security posture of their partners, the reality of the current market is that vulnerabilities can emerge and be exploited in a matter of seconds. Recent shifts in the cybersecurity industry indicate that static spreadsheets and annual audits no longer provide the necessary depth to safeguard sensitive data against sophisticated threat actors. To address this widening visibility gap, SecurityScorecard formally integrated the capabilities of Driftnet, a specialist in advanced internet scanning and threat intelligence. This strategic acquisition signaled a major transition toward real-time, threat-informed risk management that prioritized actual exposure over theoretical compliance. By merging these two distinct yet complementary technologies, the industry moved closer to a standard where hidden risks were identified before they could be leveraged by attackers.
Advancing Threat-Informed Security Architectures
Modernizing Third-Party Risk Management
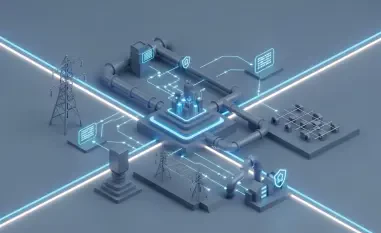
Transitioning from a reactive stance to a proactive posture required a fundamental rethink of how vendor relationships were monitored throughout their entire lifecycle. The integration of Driftnet into the TITAN AI platform allowed for a high-fidelity view of global infrastructure exposures that was previously unattainable for most security operations centers. This evolution effectively transformed the role of the Security Operations Center analyst from a passive observer of vendor scores to an active threat hunter capable of pinpointing specific weaknesses in a supplier’s network. The synergy between these platforms ensured that security teams were not just receiving alerts about potential problems but were instead provided with actionable intelligence that correlated known threats with specific assets. Such a unified perspective was essential for managing the sheer scale of modern business networks, where a single unpatched server in a distant sub-processor’s environment could lead to a catastrophic data breach for the primary organization.
Beyond technical visibility, this acquisition reinforced the concept of threat-informed third-party risk management as a necessary standard for corporate governance. Dr. Aleksandr Yampolskiy emphasized that traditional infrastructure scanning reached its limits in an environment where digital footprints were expanding faster than they could be manually documented. By adopting a system that used deep intelligence to prioritize the most critical risks, enterprises allocated their limited resources to the areas where they had the greatest impact. This approach moved away from the “check-the-box” mentality and focused on the actual probability of an exploit occurring based on real-time data feeds. Organizations found that the cost of maintaining a blind spot in the supply chain was far higher than the investment required to gain comprehensive visibility. Consequently, the push for more integrated risk management tools became a primary focus for Chief Information Security Officers who were tasked with defending complex, multi-cloud environments.
Mapping the Hidden Global Infrastructure
Technical differentiation was the cornerstone of this new capability, particularly through Driftnet’s specialized focus on non-standard port enumeration and advanced fingerprinting techniques. While conventional scanners often overlooked the “hidden corners” of the web, this technology successfully indexed approximately 40% more internet-exposed hosts than other leading intelligence providers. This increased coverage was largely due to its robust discovery mechanisms for IPv6 addresses, which became a common hiding place for misconfigured assets and shadow IT projects. By shining a light on these neglected segments of the internet, security professionals identified exposures that were previously invisible to standard reconnaissance tools. The ability to scan and analyze these non-traditional pathways was no longer a luxury but a requirement, as attackers increasingly targeted the path of least resistance. Providing this level of granularity allowed firms to verify that their partners maintained the same level of security hygiene as internal teams.
The operational advantages of this enhanced scanning capability extended directly into real-time security campaigns and threat identification efforts. When high-priority threats emerged, the integration facilitated tighter coordination between internal security teams and their external partners by flowing intelligence automatically into vendor risk assessments. For instance, if a new vulnerability was discovered in a specific industrial control system, the platform immediately cross-referenced this information against the known infrastructure of all associated vendors. This automation eliminated the lag time typically associated with manual outreach and questionnaire-based assessments, which often took weeks to complete. In an era where automated exploits are deployed globally within hours of a vulnerability disclosure, the speed of identification is the only viable defense. By creating a continuous feedback loop between threat intelligence and risk management, organizations ensured that their defensive strategies were always aligned with the current threat landscape.
Mitigating Risks in the Era of Automated Intelligence
Addressing the OpenClaw and Shadow AI Crisis
One of the most pressing challenges identified through this new technological lens was the rapid and often unmonitored proliferation of artificial intelligence tools across modern supply chains. Recent data from the Driftnet scanning engine uncovered more than 816,000 internet-exposed AI OpenClaw agent deployments, many of which were directly linked to previous security breaches. This discovery highlighted a dangerous trend where AI agents were being integrated into enterprise workflows without adequate access controls or rigorous security oversight. These automated tools, while designed to enhance productivity, often operated with elevated permissions that could be easily exploited if the underlying configuration was flawed. The lack of visibility into how third-party vendors used these AI models created a significant blind spot for any organization concerned with data integrity and privacy. Without a specialized scanning tool to detect these specific deployments, many firms remained unaware that their data was being processed by unsecured entities.
The urgency of managing AI-related risks was exacerbated by the fact that many of these deployments were part of “shadow AI” initiatives—projects started by departments outside the control of the formal IT organization. When these tools were exposed to the public internet, they became low-hanging fruit for attackers who used automated scripts to find and exploit misconfigured APIs and management interfaces. The consensus among cybersecurity leadership was that the industry had to move toward a model where AI deployments were subjected to the same level of scrutiny as traditional servers and software. SecurityScorecard’s move to incorporate this intelligence into its core platform allowed users to see exactly which vendors ran high-risk AI configurations. This transparency was vital for maintaining trust between business partners and for ensuring that the benefits of artificial intelligence did not come at the expense of enterprise security. By prioritizing these specific vulnerabilities, the combined platform provided a roadmap for securing next-generation infrastructure.
Collaborative Defense and Community Integration
Beyond the immediate commercial benefits, this acquisition reinforced a commitment to the global security community through the continuation of existing public-sector partnerships. SecurityScorecard maintained Driftnet’s collaborations with Computer Emergency Response Teams (CERTs) across the United States, the United Kingdom, and the European Union. These partnerships were critical for the early identification of large-scale infrastructure threats that could impact national security or critical industry sectors. By sharing high-fidelity scanning data with these organizations, the company contributed to a more resilient internet ecosystem where threats were mitigated at the source before they reached the enterprise level. This spirit of cooperation ensured that the latest intelligence was not just a proprietary asset but a public good that helped protect organizations of all sizes. The ability to synthesize private threat data with public-sector coordination represented a significant step forward in the collective defense strategy required in today’s economy.
The academic and research communities also played a vital role in this collaborative ecosystem, as Driftnet had long-standing relationships with universities focused on internet measurement research. These academic partnerships fostered the development of new methodologies for discovering and analyzing emerging internet trends, such as the growth of IPv6 and the changing nature of port-based scanning. By supporting this research, the organization ensured that its technology remained at the forefront of the field, drawing on the latest theoretical advancements to solve practical security problems. This dual focus on proprietary innovation and academic rigor provided a robust foundation for the future of vendor risk management. As digital supply chains continued to grow in complexity, the integration of these diverse intelligence sources became essential for staying ahead of sophisticated adversaries. This comprehensive approach to defense ensured that organizations were not just reacting to yesterday’s threats but were actively preparing for the future challenges.
Strategic Directions for Resilient Supply Chains
Security leaders who successfully navigated the integration of advanced scanning technologies realized that visibility was only the first step toward true resilience. To capitalize on these advancements, organizations began auditing their third-party ecosystems for unmanaged AI agents and shadow infrastructure that had previously gone undetected. They prioritized the remediation of non-standard port exposures and IPv6 vulnerabilities that were once considered obscure but had become primary targets for automated exploits. These professionals also transitioned away from static risk assessments in favor of dynamic, threat-informed models that leveraged real-time data feeds from global scanning engines. By aligning vendor risk management with actual threat intelligence, firms effectively reduced their attack surfaces and improved their response times during critical security events. Ultimately, the industry moved toward a more transparent and collaborative environment where security data was shared across public and private boundaries to thwart collective threats.