Security
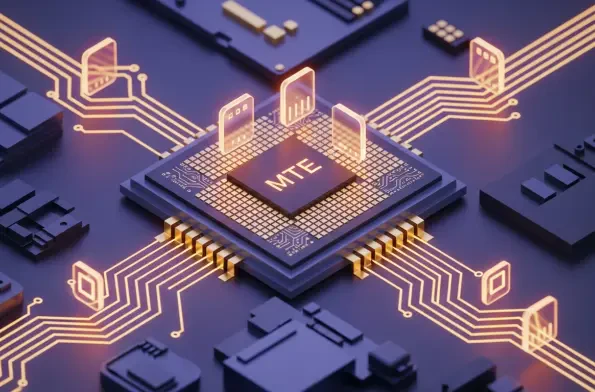
High-performance quantum computers are no longer confined to the realm of theoretical physics, as their ability to compromise classical encryption algorithms now poses a tangible risk to global digital infrastructures. While current RSA and ECC-based systems provide robust protection against

The traditional method of securing military networks by fortifying the outer perimeter has become increasingly obsolete as cyber threats evolve into more sophisticated, identity-focused attacks targeting vulnerable internal data points. To combat these shifting risks, the Defense Information

Modern cyber espionage has evolved into a sophisticated game of cat and mouse where a single unpatched line of code can grant attackers total control over a mobile device without any user interaction whatsoever. As mobile ecosystems have matured through 2026, the focus of cybercriminals has shifted
A single malicious actor equipped with nothing more than a standard laptop can effectively paralyze massive enterprise-grade data centers by exploiting a structural weakness in the HTTP/2 protocol. This specific vulnerability exploits the protocol's header compression and stream multiplexing
As the global landscape of digital threats continues to evolve with unprecedented speed, the integration of advanced generative artificial intelligence has fundamentally altered the paradigm of enterprise security for multinational life sciences organizations. The emergence of sophisticated large
The transition from traditional mechanical locking systems to interconnected digital access solutions has accelerated significantly as urban environments demand more sophisticated security protocols. Organizations no longer view a lock as merely a standalone hardware component but rather as a

1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106