Your Online Resource for the Latest News in Cybersecurity
Our picks

A profound and historically significant capital reallocation is quietly reshaping the European economic landscape, marking the most important restructuring since the formation of the single market. This transformation signals a decisive pivot away fr

A top-tier open-source intelligence analyst resigns, and overnight, a decade's worth of specialized investigative knowledge walks out the door, leaving behind nothing but a few cryptic, half-finished reports on a shared drive. For many organizations,

A comprehensive analysis of major contemporary conflicts has revealed a stark and increasingly undeniable truth: offensive cyber operations, long heralded as a revolutionary tool of statecraft, consistently fall short of their hyped potential to deli

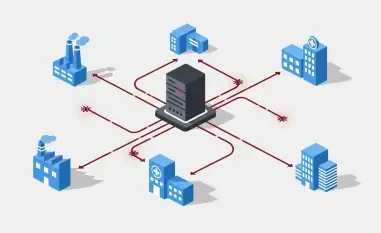
In the rapidly evolving industrial sector where the adoption of AI-driven systems and autonomous vehicles is accelerating, Cisco has distinguished itself by winning two prestigious IoT Breakthrough Awards for its forward-thinking solutions. The accol

The most significant cyber threats targeting the global financial sector are not emerging from the shadows of undiscovered zero-day exploits but are instead being delivered through highly refined, scalable, and ruthlessly efficient criminal enterpris
The seemingly secure environment of popular communication platforms has been compromised by a sophisticated, Python-based malware known as VVS Stealer, which actively targets Discord users with a formidable array of stealth and data theft capabilitie

A groundbreaking analysis from blockchain intelligence firm TRM Labs has meticulously detailed how a significant 2022 data breach at password manager LastPass directly enabled the theft of at least $35 million in cryptocurrency by Russian-linked cybe
An extensive investigation following the November 10 explosion near Delhi's Red Fort has unearthed a startlingly sophisticated terror operation, compelling the Indian government to impose sweeping new regulations on popular messaging platforms. The p

The U.S. Cybersecurity and Infrastructure Security Agency has sounded a significant alarm across the federal government and the private sector, issuing a critical directive in response to the active exploitation of a high-severity vulnerability in th

Operating from the deepest recesses of a computer's operating system where security software rarely has the final say, a newly discovered weapon has fundamentally altered the cyber espionage landscape and redefined the meaning of digital stealth. A s

The landscape of physical security is undergoing a seismic shift as two of its cloud-native pioneers, Brivo and Eagle Eye Networks, have officially combined their operations to create an undisputed giant in the industry. This strategic merger consoli

The thunderous echo of multi-billion-dollar acquisition announcements became the defining soundtrack of the cybersecurity industry this year, signaling a market transformation of historic proportions. To understand the forces driving this unprecedent

The modern cybersecurity landscape is undergoing a radical transformation, shifting from a reactive posture of building walls and responding to alarms toward a proactive strategy of preemptive defense that fundamentally alters the attacker's advantag

The perception of macOS as a secure, walled garden impenetrable to the malware plaguing other operating systems is being systematically dismantled by increasingly sophisticated threats. A newly identified variant of the MacSync Stealer, discovered by

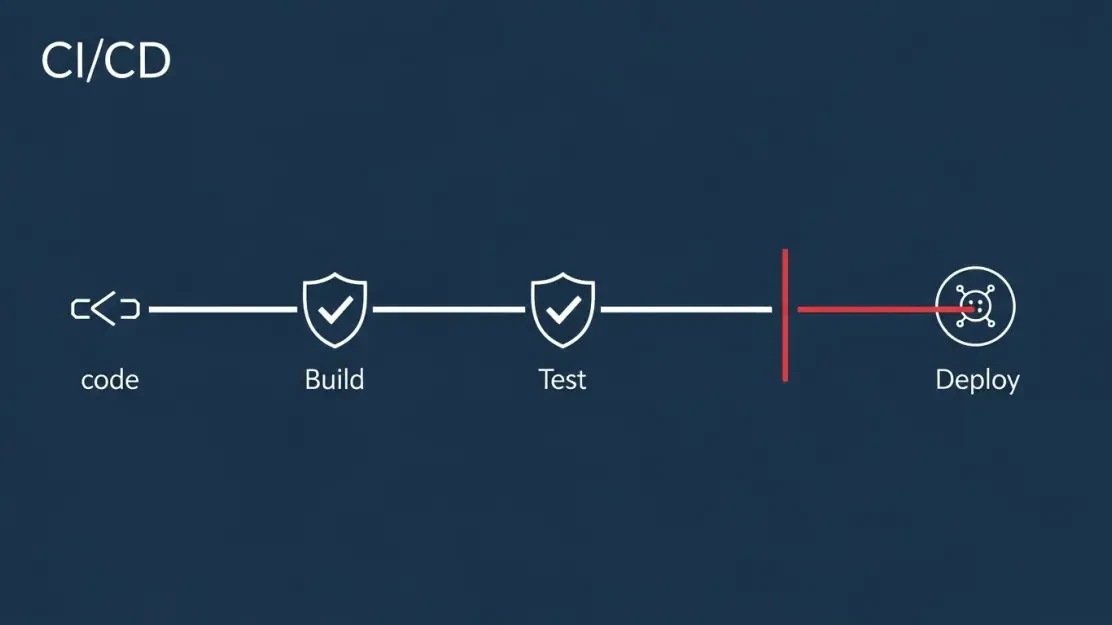
The very devices designed to be the impenetrable guardians of a network have once again become the primary gateway for sophisticated cyberattacks, turning a bastion of defense into a critical point of failure. A recently disclosed zero-day vulnerabil

The very tools millions of users trust to shield their online activities from prying eyes may be the ones actively betraying their confidence, creating a digital paradox where privacy becomes the price of admission. A startling investigation has brou