Business Perspectives
The transition from mechanical brass keys to sophisticated digital ecosystems marks a definitive break from the era when perimeter security was defined solely by the thickness of a steel door. In the current operational climate of 2026, industry reports suggest that over sixty percent of corporate
The traditional digital perimeter has dissolved into a complex web of hyper-automated vulnerabilities where malicious software no longer waits for human commands to pivot through a corporate network. As 2026 progresses, the cybersecurity landscape is witnessing a radical transformation as
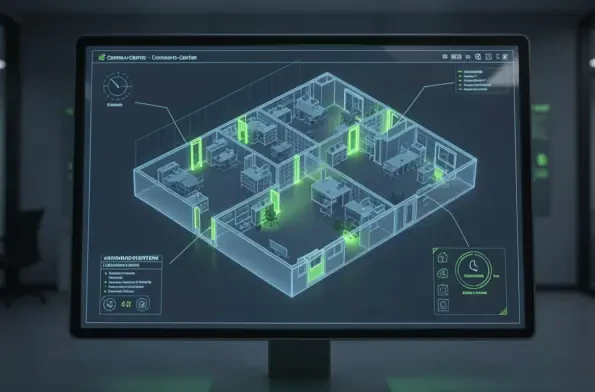
The traditional security perimeter has dissolved as modern enterprises navigate a complex ecosystem where identity, rather than physical office walls, serves as the primary gateway to sensitive digital assets and corporate infrastructure. As organizations continue to grapple with the demands of
The rapid migration of criminal activity to encrypted digital platforms has created a strategic blind spot that threatens the effectiveness of modern law enforcement agencies, necessitating a profound shift in how democratic states manage digital evidence and the legal frameworks that govern it. As

The current economic landscape in the United States reflects a volatile intersection of advanced technological integration and shifting geopolitical alliances that demand unprecedented corporate agility. Businesses today are navigating a marketplace where the traditional boundaries between physical

The contemporary digital ecosystem has transitioned from a playground for isolated hackers to a sophisticated theater of war where private enterprises find themselves caught in the crossfire of international disputes. Corporations today are no longer collateral damage in the traditional sense; they

1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86