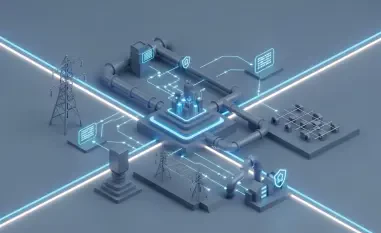
The backbone of the modern web relies heavily on hosting control panels, making the discovery of critical vulnerabilities in software like cPanel a catastrophic event for global digital infrastructure. As remote attackers shift from simple brute-force attempts to sophisticated authentication bypass techniques, the security landscape for web hosts has reached a dangerous turning point. This article examines the emergence of high-impact exploits, specifically focusing on the recent surge in automated campaigns targeting cPanel and WebHost Manager (WHM) vulnerabilities. Readers will gain insights into the methodology of elite threat actors, the technical anatomy of modern backdoors, and the long-term implications for server administrators worldwide.
The Global Surge in Automated Control Panel Exploitation
Statistical Growth and Geographic Distribution of Recent Attacks
Current data reveals a massive scale of exploitation involving over 2,000 unique IP addresses identified in automated scanning operations across the globe. These trends highlight primary points of origin for these attacks, with significant concentrations in Germany, the United States, Brazil, and the Netherlands. The evolution of authentication bypass as a preferred attack vector marks a move away from traditional credential harvesting toward exploiting direct architectural flaws. Growth metrics from firms like QiAnXin XLab show the rapid adoption of these exploits within underground communities.
Real-World Execution: The Mr_Rot13 and CVE-2026-41940 Case Study
The active exploitation of critical flaws like CVE-2026-41940 allows attackers to gain elevated, unauthorized access to hosting environments with minimal effort. This process involves a multi-stage infection chain, moving from initial shell script execution via common utilities like wget or curl to the deployment of Go-based infectors. The Filemanager payload is a sophisticated, cross-platform backdoor capable of infiltrating Windows, macOS, and Linux systems alike. Furthermore, attackers utilize malicious JavaScript injection to create fraudulent login pages, siphoning credentials directly to Telegram channels.
Expert Perspectives on Advanced Persistence and Stealth
Security researchers note the significance of dormant infrastructure, observing that some threat actors have operated undetected since 2023. Expert analysis of the Filemanager backdoor highlights its versatility, offering comprehensive file manipulation and remote shell functionality that bypasses traditional detection. Obfuscation techniques, such as the use of the ROT13 cipher for command-and-control domains, help these actors evade automated security filters. These low detection rates present a significant challenge for identifying indicators of compromise in highly customized environments.
Future Implications for the Web Hosting Industry
Control panel exploits have transitioned from singular breaches to launchpads for secondary malicious activities, including botnet propagation and ransomware deployment. This shift introduces the threat of unauthorized cryptocurrency mining, where stealthy backdoors drain server resources over long periods without being noticed. The anticipated evolution of cross-platform malware suggests a trend toward more modular tools designed to target diverse server architectures simultaneously. Administrators face long-term challenges in maintaining Zero Trust environments when the central management software is compromised.
Securing the Future of Web Infrastructure
The critical threat posed by authentication bypass exploits required a proactive response from hosting providers to secure the future of web infrastructure. Immediate patching and the implementation of multi-factor authentication served as the primary methods to mitigate these risks effectively. By prioritizing vulnerability management and rigorous system monitoring, administrators established a more resilient defense against the next generation of automated cyberattacks. This shift toward active defense mechanisms helped preserve the integrity of global hosting services.