Vulnerability Assessment
The digital landscape in 2025 is under siege as ransomware threats evolve at an alarming pace, with LockBit standing out as a major concern due to its formidable comeback with the advanced 5.0 variant, codenamed 'ChuongDong.' Reports confirm that a dozen organizations across multiple
In an era where cybersecurity threats loom larger than ever, the discovery of severe vulnerabilities in widely used networking equipment has sent shockwaves through the tech community, raising urgent questions about the safety of business and personal data. Researchers at Forescout’s Vedere Labs h

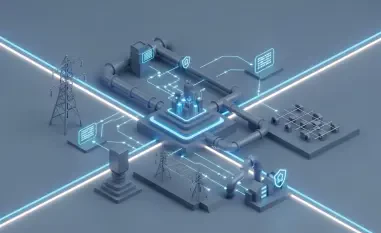
In an era where digital connectivity underpins nearly every facet of industrial operations across the European Union, a staggering statistic emerges: nearly one-fifth of cyber threats now target operational technology (OT) systems, critical for managing industrial control systems and

In an era where global navigation satellite systems (GNSS) underpin nearly every facet of modern life, from guiding airplanes through crowded skies to ensuring farmers plant crops with precision, a shadowy threat looms large on the horizon, challenging the very foundation of our technological

In a world where digital collaboration tools are the backbone of modern enterprises, a hidden battle unfolds as cybercriminals exploit trusted systems to infiltrate sensitive networks, leaving organizations vulnerable. Picture a telecommunications giant in the Middle East or a university in the

In a world where digital deception can unravel national security, consider the chilling scenario of a single email, seemingly from a trusted embassy, infiltrating an entire government network with devastating precision, a tactic expertly wielded by MuddyWater, an Iranian-linked cyber espionage