Identity & Access Management
The monthly ritual of software updates often feels like routine maintenance, but the latest security bulletin from Microsoft serves as a stark reminder of the persistent and evolving threats lurking in the digital landscape. February’s Patch Tuesday release addressed approximately 60 security f

The intricate digital architecture underpinning a nation’s connectivity became the silent battleground for an 11-month clandestine war, culminating in Singapore’s successful disruption of a sophisticated state-sponsored espionage campaign. This extended engagement, codenamed "Operation Cyber Gu

We're joined today by Malik Haidar, a cybersecurity expert who has spent years on the front lines protecting multinational corporations from complex threats. With a deep background in analytics and intelligence, Malik brings a unique business-focused perspective to the rapidly evolving world

The long-standing tension between stringent cybersecurity measures and the demand for fast-paced, collaborative workflows has defined a critical challenge for modern enterprises. The integration of Privileged Access Management (PAM) into collaborative platforms represents a significant advancement

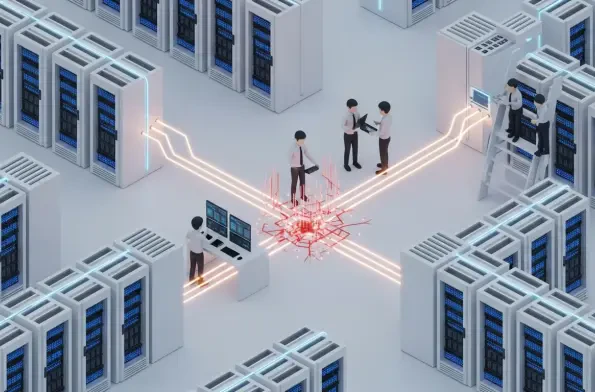
The lines once drawn by firewalls and network gateways have evaporated, leaving behind a digital landscape where the only constant, the only true defensible border, is the identity of who or what is accessing critical data. The cybersecurity industry has reached an inflection point, a moment

A subtle but critical security flaw recently placed over 40,000 WordPress websites in jeopardy, stemming from a popular tool designed for engagement and data collection. The Quiz and Survey Master (QSM) plugin, widely used for creating interactive content, was found to contain a significant SQL