The British cybersecurity landscape is currently navigating a period of unprecedented expansion, with the industry reaching a record annual valuation of £14.7 billion as of 2026. This surge is characterized by a significant 17% increase in the gross value added to the national economy, which now stands at £9.1 billion, supported by a specialized workforce that has grown to nearly 70,000 employees. Data reveals that there are now 2,603 active firms operating within this high-stakes sector, representing a 20% year-on-year increase. Most notably, the market has witnessed a 68% jump in businesses specifically dedicated to providing artificial intelligence-focused security solutions. This rapid industrial growth occurs against a backdrop of escalating digital risks, where the complexity of attacks is evolving as quickly as the defensive tools designed to stop them. The convergence of economic prosperity and heightened vulnerability has placed the United Kingdom at a critical juncture where technological innovation must outpace the sophisticated capabilities of global threat actors to ensure long-term stability.
Strategic Shifts: The Drive for National Cyber Resilience
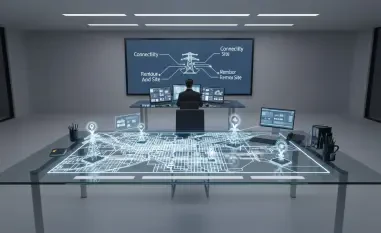
The government has responded to this evolving threat landscape by introducing the Cyber Resilience Pledge, a strategic initiative unveiled during the CYBERUK conference to strengthen the nation’s digital perimeter. This program fundamentally changes how organizations approach security by demanding that cybersecurity be elevated to a board-level priority rather than being treated as a secondary IT concern. By encouraging firms to integrate the National Cyber Security Centre’s Early Warning Service into their operations, the initiative aims to create a proactive defense network capable of identifying vulnerabilities before they are exploited. Furthermore, the push for mandatory Cyber Essentials certification across entire supply chains addresses the reality that a company is only as secure as its weakest external partner. While these measures are framed as essential for maintaining national competitiveness, the voluntary nature of the pledge has sparked debate among industry analysts regarding its sufficiency in the face of persistent state-sponsored activities.
Building on the foundation of public-private cooperation, the current strategy emphasizes the necessity of transparency and shared intelligence to combat coordinated digital assaults. Large-scale enterprises are now expected to lead by example, demonstrating that robust security protocols are a prerequisite for participating in the modern global economy. This shift in organizational culture is intended to move the industry away from reactive troubleshooting toward a state of continuous readiness. However, the transition is not without its challenges, as smaller firms often struggle with the financial and technical burden of meeting these rigorous new standards. To bridge this gap, the government is facilitating mentorship programs and providing resources to ensure that the entire ecosystem remains resilient. The overarching goal is to create a unified front where technical excellence and strategic governance work in tandem to protect critical infrastructure, thereby securing the digital foundations upon which the nation’s future prosperity depends.
Technological Frontiers: Countering the Rise of Generative AI Threats
The defensive paradigm is undergoing a radical shift as powerful new models such as Mythos Preview and GPT-5.5 redefine the capabilities of both attackers and defenders. The AI Security Institute has issued warnings that these advanced systems are being evaluated for their potential to breach even the most well-defended networks, necessitating a transition to what experts call machine-speed security. This approach involves the deployment of automated vulnerability scanning and real-time threat detection systems that can respond to incidents in milliseconds, far faster than any human operator could manage. Additionally, there is a significant movement toward adopting memory-safe programming languages and systems to eliminate entire classes of vulnerabilities that have plagued software for decades. As AI models become more adept at identifying and exploiting code flaws, the reliance on traditional manual patching is being replaced by autonomous defensive agents capable of self-healing and dynamic reconfiguration.
As the integration of AI into security operations becomes the standard, the focus is expanding from simple detection to the anticipation of complex, multi-stage attacks. Machine learning algorithms are now trained to recognize the subtle behavioral patterns of sophisticated malware that might otherwise bypass signature-based filters. This evolution requires a massive investment in data engineering to ensure that security tools are fueled by high-quality, diverse datasets that reflect the current threat environment. Moreover, the industry is grappling with the dual-use nature of AI, where the same innovations that power defensive breakthroughs are also being repurposed by cybercriminals to automate phishing campaigns and generate polymorphic code. To stay ahead, cybersecurity firms are increasingly leveraging generative models to simulate attack scenarios, allowing them to stress-test systems against hypothetical threats that have not yet appeared in the wild. This proactive stance is essential for maintaining the integrity of financial systems and public services in an era of automated warfare.
Legislative Frameworks: Enhancing Accountability and Global Standards
Policymakers have reached a consensus that the rising costs associated with inaction, particularly in the realm of ransomware, have become economically unsustainable for the state. In response, the introduction of the Cyber Security and Resilience Bill marks a transition from voluntary guidance to a more stringent regulatory environment. This legislation is designed to tighten oversight of essential service providers by mandating the reporting of all major digital incidents and increasing the accountability of Managed Service Providers who handle critical data. By imposing legal obligations on these entities, the government aims to ensure that no single point of failure can jeopardize the functionality of the power grid, healthcare systems, or transportation networks. This legislative trajectory is not happening in isolation; it mirrors international efforts in the United States and the European Union, suggesting a move toward a harmonized global framework that holds malicious actors accountable while protecting essential public interests.
Looking ahead, organizations must move beyond compliance-based security to embrace a model of radical accountability and cross-border collaboration. The immediate next step for industry leaders involves the implementation of zero-trust architectures that assume every user and device is a potential threat until proven otherwise. This practical application of security principles will be augmented by the development of international data-sharing treaties, allowing nations to pool resources and intelligence against transnational cybercrime syndicates. Investors and stakeholders should prioritize firms that demonstrate not just technological prowess, but also a commitment to ethical AI development and robust governance structures. As the sector continues to serve as both a major economic driver and the frontline of national defense, the focus will remain on building a sustainable infrastructure that can withstand the pressures of an increasingly volatile digital world. Ultimately, the success of these measures was determined by the ability of the legal system to evolve at the same pace as the technology it sought to regulate.