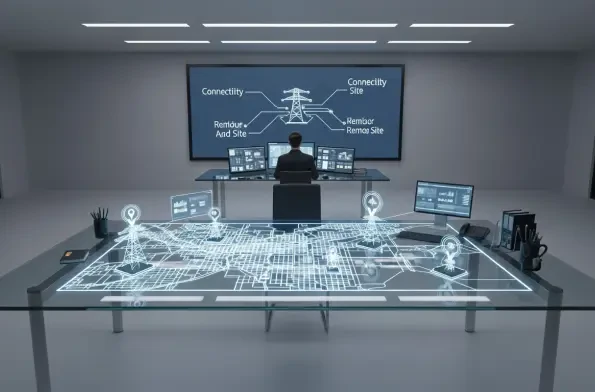
Modern security for critical infrastructure involves much more than simply bolting a gate shut; it requires a digital consciousness that monitors every entry point across vast geographical distances. As industrial landscapes expand, the reliance on mechanical keys has become a liability rather than an asset. The transition to ABLOY CUMULUS reflects a fundamental shift toward intelligent, connected ecosystems where physical durability meets sophisticated software.
This evolution is a direct response to the massive challenge of securing thousands of miles of utility lines and remote substations without the logistical nightmare of physical key management. By embracing a cloud-based approach, operators can now replace heavy key rings with encrypted digital credentials. This change mirrors the broader digital transformation seen across industrial safety, where the goal is to create a seamless fabric of protection that covers both the physical and virtual realms.
The Evolution of Industrial Access Control: From ABLOY BEAT to CUMULUS
The strategic pivot of ALCEA and ASSA ABLOY toward software-driven security highlights a significant milestone in the history of access control. What began as the ABLOY BEAT keyless padlock has matured into a unified cloud platform known as CUMULUS. This rebranding signifies a move beyond a single hardware product toward a comprehensive service model that prioritizes connectivity and real-time oversight for complex organizations.
Historical contexts show that yesterday’s solutions often struggled with the fragmentation of data across different sites. Today, the growing demand for visibility in the telecommunications, energy, and transportation sectors has forced a consolidation of security assets. By integrating these once-isolated hardware pieces into a centralized system, the CUMULUS platform provides a single pane of glass for managing access rights across an entire national grid or transportation network.
A Deep Dive into the ABLOY CUMULUS Ecosystem and Technical Capabilities
Maintaining the highest standards of hardware ruggedness remains a cornerstone of the CUMULUS identity. Every lock is engineered to survive extreme environments, featuring IP68-rated protection and hardened steel construction that resists both tampering and the elements. This physical toughness ensures that even the most remote cell towers or water treatment facilities remain secure against forced entry, regardless of the weather conditions.
However, the true power of the platform lies in its digital intelligence and flexibility. Utilizing Bluetooth technology and mobile credentials, the system allows technicians to gain site entry through their smartphones, eliminating the risk of lost or stolen keys. Furthermore, the use of open REST APIs enables enterprise managers to connect security data directly with their existing maintenance and management software, creating a synchronized operational environment.
Bridging the Gap: Physical Hardness and Digital Visibility
Modern operators have shifted their priorities, now valuing data-driven insights just as much as the strength of a padlock. The ability to see who accessed a site, and for how long, provides a level of accountability that was previously impossible. This visibility is crucial for global utilities that must prove compliance with strict safety regulations while simultaneously minimizing the operational risks associated with unauthorized access.
Connectivity plays a vital role in maximizing uptime for geographically dispersed assets like electrical substations and well pads. When security events are captured and reported in real time, managers can respond to potential breaches or maintenance issues instantly. This proactive stance ensures that infrastructure remains operational and that technicians are protected by a system that knows exactly where they are and what permissions they hold.
Implementing Scalable Security Frameworks for Remote Industrial Sites
Implementing a mobile-first security design is the most effective strategy for managing large teams of field technicians across diverse locations. By deploying CUMULUS, organizations integrated high-level security into their current operational workflows without causing friction. This streamlined approach ensured that safety protocols were followed naturally, as the digital credentials were tied directly to the technician’s work orders and scheduled tasks.
Scalability was achieved by removing the administrative overhead typically associated with traditional locking systems. Organizations expanded their security coverage across thousands of remote access points with ease, allowing for a future-proof framework that grew alongside the infrastructure. Industry leaders then looked toward further automating access permissions through AI-driven analytics to predict and prevent security vulnerabilities before they manifested.