Modern industrial systems are no longer isolated islands of mechanical logic but have transformed into hyper-connected digital ecosystems that drive the pulse of global civilization. As critical national infrastructure sectors like energy, water, and advanced manufacturing embrace digital transformation, the once-impenetrable air gap between information technology and operational technology has effectively vanished. This integration has birthed a new era of efficiency while simultaneously exposing high-stakes production environments to a range of sophisticated cyber threats that were previously restricted to the corporate office.
The shift toward a hyper-connected landscape means that a vulnerability in a business email server can now serve as a gateway to a turbine controller or a water treatment valve. Market dynamics have shifted accordingly, as industrial operators and their engineering partners now find themselves navigating a complex web of specialized security vendors. These new players provide niche tools designed specifically for industrial control systems, yet the fundamental challenge remains the integration of these tools into legacy environments that were never designed for internet connectivity.
The Converging Worlds of IT and OT: A New Era for Critical Infrastructure
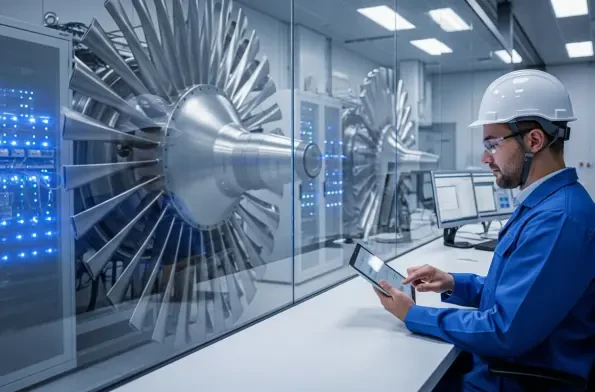
The modern industrial landscape is defined by the seamless flow of data between the factory floor and the cloud, a transition that has redefined the meaning of critical national infrastructure. While this connectivity enables real-time optimization and predictive maintenance, it also creates a massive, unified attack surface that spans across geographic and digital boundaries. The historical isolation of these systems provided a layer of security through obscurity, but the current demand for data-driven insights has forced a reconciliation between the fast-paced world of software and the rigid, safety-first world of heavy machinery.
Analyzing the significance of this vanishing air gap reveals a profound change in how risk is managed within the industrial sector. Digital transformation has effectively turned physical assets into networked nodes, making them susceptible to the same lateral movement tactics used in traditional data breaches. Engineering partners, who once focused solely on mechanical performance, must now act as the first line of defense, ensuring that the hardware they install does not become a permanent backdoor for malicious actors.
The Escalating Threat Horizon and Industrial Growth Projections
Analyzing Current Attack Trends and Shifting Adversary Behaviors
The rise of industrial ransomware has become the most pressing concern for global supply chains, with recent data indicating a 64 percent surge in attacks targeting production environments. Specialized threat groups have multiplied, with active organizations growing from 80 to 119 over the last year, collectively impacting over 3,300 organizations worldwide. This proliferation suggests that adversaries are no longer just opportunistic; they are increasingly focused on the specific protocols and hardware that govern physical processes.
Manufacturing has emerged as the primary target for these extortionists due to its extreme sensitivity to downtime. Unlike a corporate office where a few days of system outages might be managed, a production line stoppage results in immediate, compounding financial losses. Attackers recognize this leverage and have shifted their tactics to target engineering workstations and upstream suppliers. By infiltrating the supply chain, they can achieve a cascading impact, potentially compromising multiple high-value targets through a single, well-placed entry point.
Forecasting the Future of Industrial Resilience and Market Expansion
Market projections for operational technology security suggest a pivot from reactive, emergency spending toward a more strategic investment in long-term cyber resilience between 2026 and 2028. This shift is driven by the realization that intermittent patches are no longer sufficient to protect the integrity of global operations. Organizations are beginning to prioritize specialized detection capabilities that can identify anomalies in industrial protocols before they manifest as physical failures.
Data-driven performance indicators highlight that heightened threat activity is forcing a permanent change in how industrial budgets are allocated. As global threat actors become more proficient in targeting industrial control systems, the market for specialized security services is expected to expand significantly. Companies that invest in deep visibility and automated threat hunting today will likely see a significant reduction in the long-term costs associated with breach recovery and operational disruption.
Overcoming the Economic Paradox and Technical Barriers in Heavy Industry
A dangerous economic paradox exists within heavy industry where security budgets are often the first to be cut during periods of fiscal tightening. Because the primary benefit of effective security is the absence of a crisis, these benefits remain invisible to stakeholders until a failure occurs. This mindset leads to the relaxation of vendor checks and the expansion of unmonitored remote access tools, creating a fertile ground for intruders who wait for the moment of maximum vulnerability to strike.
Legacy system vulnerabilities present a unique technical hurdle, as much of the equipment currently in use was built long before cybersecurity was a design requirement. Securing unpatched hardware without disrupting 24/7 operations requires a delicate balance of network isolation and compensating controls. Furthermore, the complexity of recovery in an industrial setting involves rigorous safety protocols that can delay the restoration of services for weeks, far exceeding the time and cost associated with standard IT recovery.
Navigating the Regulatory Landscape and Standardizing Industrial Defense
Adopting established frameworks, such as the SANS Five Critical Controls, provides industrial operators with a proven blueprint for a defensible posture. These guidelines emphasize the importance of focused, high-impact activities like incident response and secure remote access rather than chasing every possible vulnerability. By concentrating on these fundamentals, organizations can build a resilient foundation that withstands the majority of contemporary threats without overcomplicating their operational workflows.
Emerging national and international regulations are increasingly acting as a catalyst for this change, mandating baseline security standards for anyone managing essential services. Compliance is moving from a voluntary checkbox to a legal necessity, forcing industrial cyber risk into the boardroom. Executive oversight has become crucial, as business continuity now depends as much on digital integrity as it does on mechanical reliability or fuel supply.
Future-Proofing Industrial Operations Against Systemic Risk
Prioritizing visibility and network segmentation remains the most effective strategy for future-proofing industrial assets against systemic risk. By maintaining a deep, real-time inventory of all connected assets and isolating critical network zones, operators can effectively contain breaches and prevent them from spreading to the production floor. This architectural approach ensures that even if one part of the network is compromised, the core industrial processes remain shielded from interference.
Automation and proactive monitoring technologies are beginning to play a larger role in detecting the subtle lateral movements that precede a major attack. These systems can identify unauthorized changes to controller logic or unusual data flows that might indicate an intruder is mapping the environment. Building a culture of resilience requires a unified effort between IT and OT teams, ensuring that recovery protocols are not just written on paper but are regularly tested under realistic conditions.
Closing the Gap Through Disciplined Fundamentals and Strategic Investment
The investigation into the industrial cyber security gap revealed that the most successful defensive strategies were rooted in disciplined, steady practices rather than the adoption of complex technical solutions. It was found that organizations which prioritized asset visibility and rigorous access management were significantly better positioned to withstand the surge in ransomware activity. The data indicated that the widening gap between threat sophistication and defensive capability was often bridged not by massive spending, but by a cultural shift toward operational resilience.
Stakeholders were encouraged to view security as an essential component of uptime and to move away from the habit of treating it as a discretionary expense. The report highlighted that the long-term economic stability of global supply chains depended on the ability of critical national infrastructure operators to maintain operational integrity in the face of constant digital probing. Ultimately, the transition toward a more secure industrial future required a commitment to the fundamentals of network hygiene and executive-led governance to ensure that the progress of digital transformation was not undone by preventable vulnerabilities.