Hackers & Threats
The contemporary digital landscape is currently defined by a volatile and widening gap between the discovery of system flaws and the capacity of organizations to implement effective defenses. This week's cybersecurity developments highlight a messy reality where foundational security advice is
The digital trust that underpins the global software ecosystem is under siege as threat actors shift from targeting individual companies toward poisoning the very tools used to secure them. This paradigm shift represents a fundamental transformation in cyber warfare, where the defensive perimeter
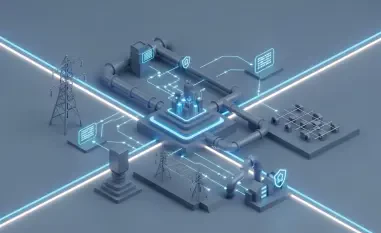
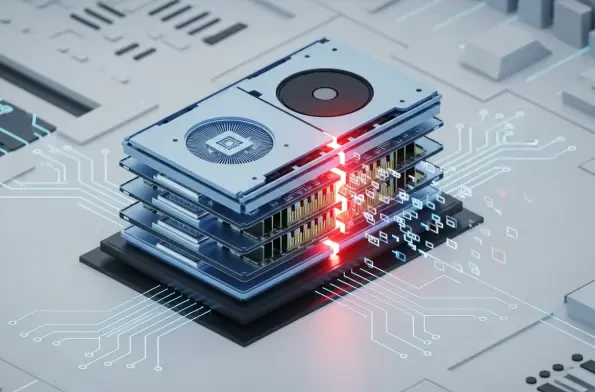
The digital architecture of the modern enterprise is currently undergoing a radical transformation that has effectively rendered the traditional concept of a protected perimeter obsolete. Instead of a single fortified gate, organizations now operate within a massive, interconnected web of

The historical boundary separating peripheral hardware from core system authority has dissolved as researchers demonstrate that high-performance graphics processors can be coerced into betraying their host systems through silicon-level manipulations. This transformation, catalyzed by the GPUBreach
The silent subversion of a digital pillar often occurs not through a frontal assault on its core code but through the subtle manipulation of the very pathways users trust to deliver it. For nearly two decades, hardware enthusiasts and system administrators have relied on the CPUID website as a gold

The digital landscape has shifted from the era of loud, disruptive explosions of data theft to a much quieter and more dangerous period of persistent infiltration that targets the very trust users place in their everyday tools. This transformation marks a fundamental departure from the high-profile