Hackers & Threats
The persistent cat-and-mouse game between digital defenders and malicious actors has reached a fever pitch, where human speed is no longer sufficient to secure the expanding global attack surface. Anthropic has stepped into this breach with Project Glasswing, a specialized cybersecurity initiative

Digital shadows often hide in plain sight, transforming the very tools we use for global connection into precision instruments for state-sponsored espionage. Recent investigations into APT37, a persistent threat actor also known as ScarCruft, reveal a sophisticated pivot in their operational

A quiet home office in downtown São Paulo recently became the silent ground zero for a sophisticated digital heist that bypassed every modern security layer installed on the victim’s computer. This incident was not an isolated failure but part of a sweeping wave of attacks across Brazil and Mexico,

Every single day, thousands of employees log into secure corporate portals, believing that a successful biometric scan or a hardware security key press has rendered their digital identity impenetrable for the duration of their shift. This sense of security, while comforting, often overlooks a

The traditional concept of a "secure perimeter" has become an artifact of the past as modern software pipelines now face an onslaught of invisible, automated threats that strike from within the very tools used to build them. This shift was never more apparent than during the recent

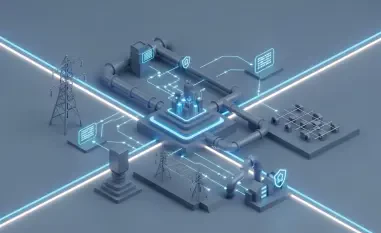
The arrival of a new era in cyber warfare means that the time required for an attacker to pivot from a single point of entry to full system compromise is now measured in fleeting seconds rather than days or hours. This acceleration represents a paradigm shift that renders traditional, human-centric