Malware Analysis
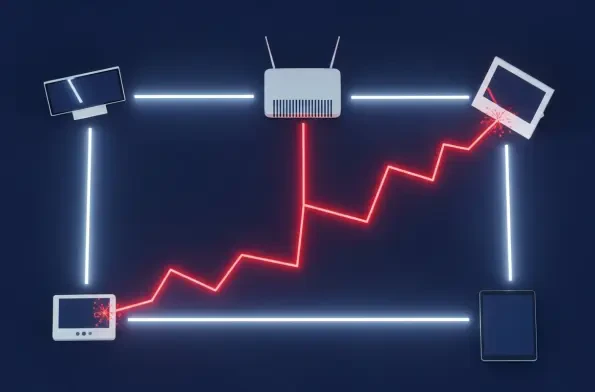
A deeply troubling security advisory has revealed the emergence and explosive growth of a sophisticated malware operation that shatters the foundational assumption of home network security, proving that devices operating behind a standard router are no longer inherently safe from external threats.
The Urgent Threat to Your Email Security Infrastructure A recently disclosed zero-day vulnerability in Cisco's email security gateways has sent shockwaves through the cybersecurity community, revealing a sophisticated espionage campaign that went undetected for months. Identified as

A sudden and inexplicable browser crash is often dismissed as a frustrating but benign technical glitch, yet a new cyberattack campaign is turning this common annoyance into a highly effective weapon for corporate infiltration. A comprehensive analysis of this sophisticated threat, dubbed

The professional trust meticulously built on platforms designed for networking and career advancement is now being systematically weaponized as the new delivery mechanism for sophisticated cyber threats. For years, the corporate world has fortified its email gateways, training employees to spot the

A highly sophisticated state-sponsored threat actor, with suspected ties to China, has been systematically targeting critical infrastructure organizations across North America for at least the past year, leveraging a dangerous combination of previously unknown software vulnerabilities and readily

In an ironic twist that highlights the fragile operational security within the cybercriminal underworld, a prolific hacker specializing in data theft recently became a victim of the very same tactics they employed against countless others. Security researchers have successfully turned a popular