Cyber Risk Management
Malik Haidar has spent years inside multinational firms chasing down intrusions, deconstructing adversary tradecraft, and turning raw telemetry into board-ready decisions. He blends analytics, intelligence, and security with a sharp business lens, the kind you need when thousands of devices can go

Windows RPC Trust Boundaries, Market Actors, and Why PhantomRPC Resonates Now When privileged Windows clients reach for familiar RPC servers that happen to be missing, the runtime’s willingness to accept a substitute responder can turn a routine call into an identity handoff that elevates l

Financial Services at an AI Crossroads: Scale, Interdependence, and Exposure Lightning-fast automation has collapsed the gap between bug discovery and breach execution, and finance now runs across rails so tightly coupled that a single fault can echo from payments to trading in minutes. Payments,

The Evolution of Federal Cyber Defense and the Rise of Managed Risk The current security environment represents a complex web where the ghosts of legacy code frequently collide with the rapid-fire innovations of modern cloud infrastructure. As cyber threats transition from opportunistic probes to
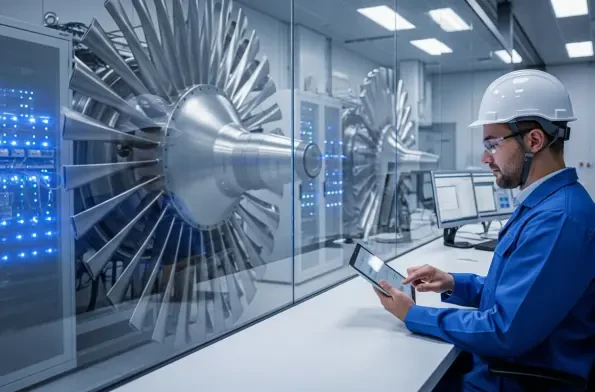
Modern industrial systems are no longer isolated islands of mechanical logic but have transformed into hyper-connected digital ecosystems that drive the pulse of global civilization. As critical national infrastructure sectors like energy, water, and advanced manufacturing embrace digital
The digital footprints left behind by modern communication platforms have long been a focal point for federal investigators seeking to reconstruct private dialogues that users believed were permanently erased from their devices. Recent disclosures regarding a vulnerability tracked as CVE-2026-28950









