Cyber Risk Management
The Shift Toward Threat-Informed Exposure Management For many years, the global cybersecurity industry operated under the persistent delusion that patching every single software vulnerability was a feasible or even desirable strategy for modern enterprise defense. This reactive posture, while

The New Frontier of Hardware Security and Display Integrity While digital firewalls and encrypted servers have long defined the parameters of corporate defense, a subtle and dangerous vulnerability remains hidden within the cables that connect workstations to their displays. Modern hackers have

The seamless integration of autonomous intelligence into the foundational layers of coding environments has fundamentally shifted the baseline for technical productivity in the current year. The Google Antigravity Platform emerges as a sophisticated response to the limitations of traditional

Moving Beyond Compliance: The Shift to Proactive Defense The modern financial sector is currently grappling with a fundamental paradigm shift where the ability to survive a cyberattack has become more valuable than the simple attempt to prevent one. For decades, the industry relied on a defensive

Deep within the digital architecture of the modern global enterprise, a new generation of autonomous software entities is performing critical operations without a single human administrator realizing they even exist. While IT departments focus on securing endpoints and firewalls, a new class of

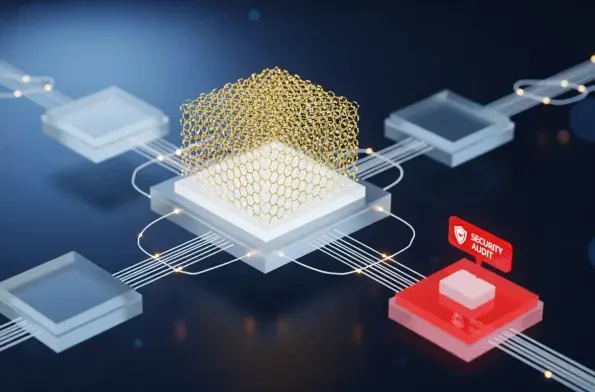
The modern software development lifecycle relies heavily on a complex web of interconnected cloud services, but a recent security breach at Vercel has demonstrated how a single weak link in this chain can expose entire organizational infrastructures to sophisticated threat actors. The incident