Hackers & Threats
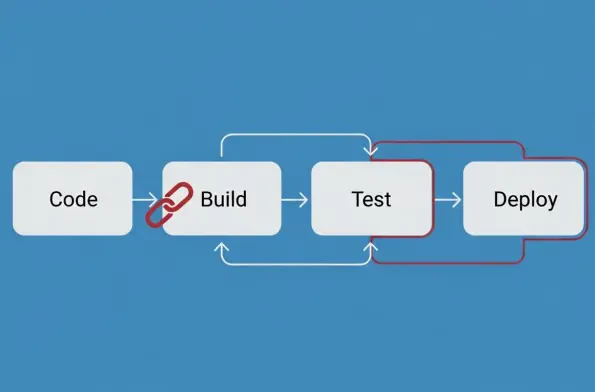
The year 2025 will be remembered in cybersecurity circles not just for the record-breaking volume of new vulnerabilities disclosed but for the strategic precision with which threat actors exploited them to undermine the global software supply chain. An unprecedented surge in Common Vulnerabilities
The unassuming smart TV in the corner of the living room, once a symbol of modern convenience, has quietly become a soldier in a colossal cyber army, following the discovery of the Kimwolf botnet. This sprawling network, comprising an estimated 1.8 million devices, signals a new era in cyber

A chilling demonstration has cast a long shadow over the rapid advancements in humanoid robotics, revealing a critical vulnerability that allows these sophisticated machines to be covertly seized and controlled through simple spoken words. The breakthrough research, presented by the cybersecurity
For the first time in the recent history of cyber warfare, the coordinated efforts of international law enforcement agencies are beginning to pierce the veil of the anonymous digital underworld, transforming elusive digital phantoms into defendants standing in physical courtrooms. Recent victories,

A seemingly routine message to an accounts payable department, complete with a convincing email reply chain, is often the first and only indicator of an attack by a highly disciplined global fraud syndicate. This research investigates the Scripted Sparrow gang, a highly organized Business Email

The recent apprehension of the central developer behind the notorious RaccoonO365 phishing platform in Nigeria serves as a potent illustration of a paradigm shift in the global fight against cybercrime. This single arrest, while significant, represents a much larger and more crucial trend: the