Malware Analysis
The simple, convenient act of tapping a payment card to a smartphone has been ingeniously weaponized by a sophisticated cyber campaign, transforming a feature designed for ease of use into a silent tool for financial theft. A new and highly evasive form of Android malware, dubbed "Ghost

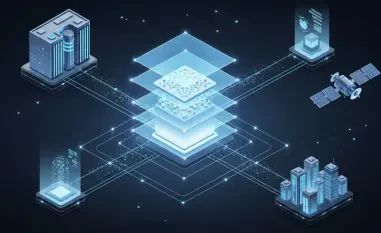
The very tools designed to streamline operations and connect disparate systems can sometimes harbor hidden doorways for malicious actors, transforming a trusted automation hub into a significant security liability. A newly discovered vulnerability in the n8n platform serves as a stark reminder of
A recently disclosed vulnerability within a widely used Dolby audio component has put a vast number of Android devices at risk, prompting Google to issue an urgent security directive as part of its January 2026 Android Security Bulletin. The critical flaw, if successfully exploited, could allow
A recently discovered vulnerability within Zoom's widely used Windows client created a significant security risk, potentially allowing malicious actors to steal sensitive data and gain unauthorized control over affected systems. The flaw, which was reportedly exploited in the wild before a
Analyzing the Threat: An Introduction to VVS Stealer The proliferation of sophisticated cybercrime tools has reached a critical point, where powerful malware is no longer the exclusive domain of elite hacking groups but is available to a much broader audience of malicious actors. This review
The smartphone in your pocket has become the central hub of modern life, acting as your digital wallet, personal communicator, and identity verification tool all in one, making its security an issue of paramount importance. As our integration with these devices deepens, the threats designed to