Cyber Risk Management
With a deep background in securing multinational corporations against digital and physical threats, Malik Haidar has a unique vantage point on how analytics and intelligence can reshape industries. He specializes in integrating robust security frameworks with core business objectives, making his
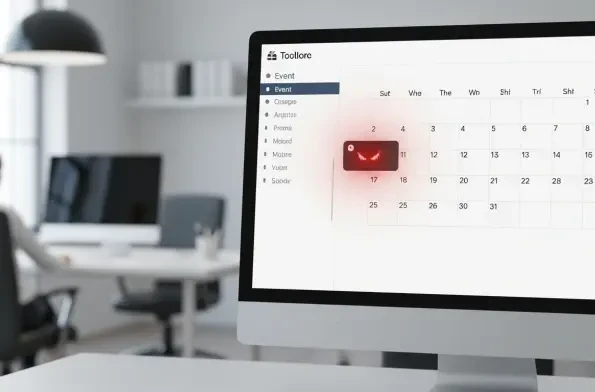
A seemingly innocent calendar notification pops up, but behind its benign appearance lies a sophisticated attack capable of granting a remote actor complete control over a user's computer system. This is not a hypothetical scenario but a demonstrated reality, highlighting a severe, zero-click
In a world where our entire lives are on our phones, the threat of mobile spyware has never been more immediate. We're joined today by Malik Haidar, a veteran cybersecurity expert who has spent his career on the front lines, battling sophisticated threats within major corporations. He's
System administrators faced a formidable challenge this February as a wave of critical security updates demanded immediate attention, headlined by Microsoft's disclosure of six zero-day vulnerabilities already being actively exploited in the wild. This sudden influx of patches, addressing a

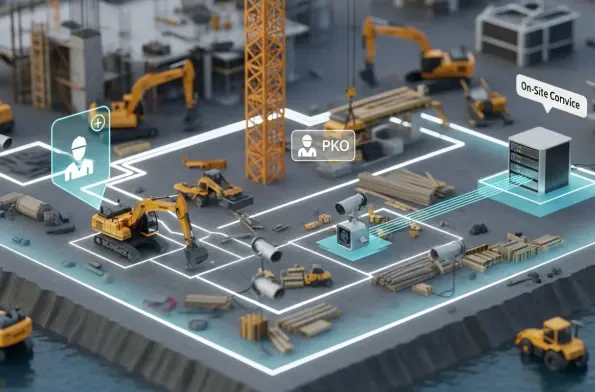
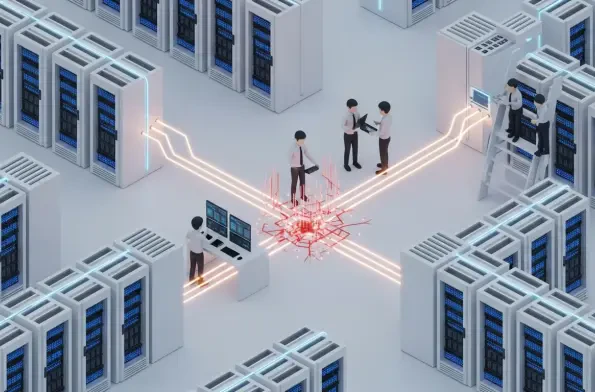
The coordinated cyberattack against European government institutions, which exploited critical vulnerabilities in Ivanti's mobile management software, has sent a clear and chilling message about the fragility of digital supply chains in the public sector. A sophisticated campaign struck at the
A recently disclosed vulnerability within the globally deployed Roundcube webmail software has demonstrated how obscure features in common web standards can be manipulated to completely neutralize fundamental email privacy protections. Security researcher Null Cathedral revealed a sophisticated