Compliance & Regulations
The healthcare payer information technology sector is undergoing a fundamental and rapid transformation, with the year 2026 emerging as a critical inflection point for execution and modernization. Survey findings from Black Book Research, involving over a thousand payer IT and administrative

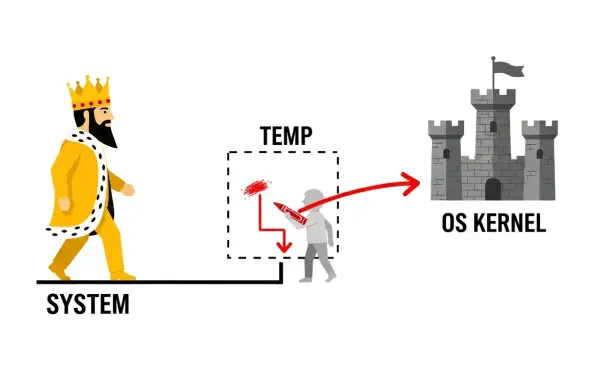
A newly disclosed vulnerability in widely used web development frameworks is enabling unauthenticated attackers to achieve complete server compromise with a single, specially crafted web request, creating an urgent and severe risk for countless enterprise applications. Identified as React2Shell
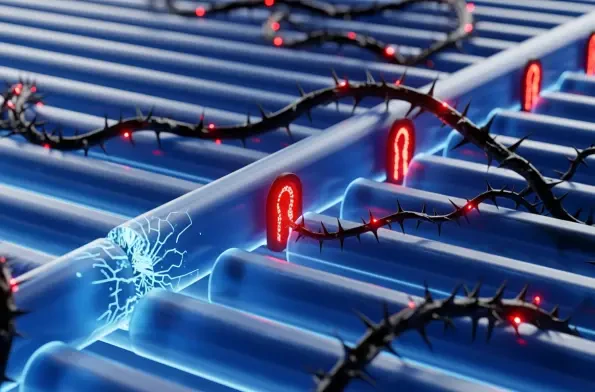
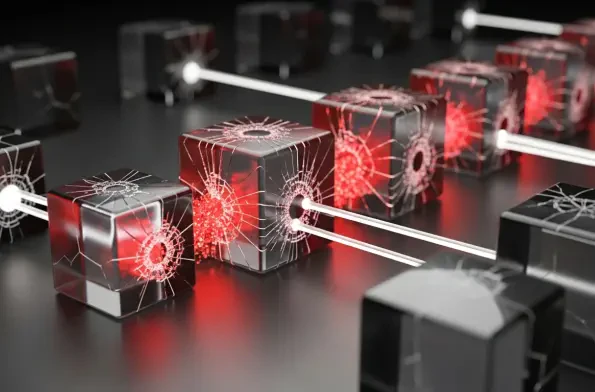
The intricate digital infrastructures that underpin modern society are facing an unprecedented and increasingly sophisticated barrage of threats, forcing a critical re-evaluation of long-held security doctrines. Recent gatherings of top industry professionals have solidified a consensus that the

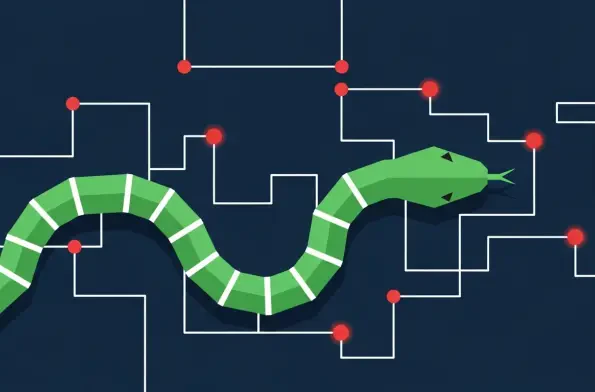
A threat actor's decision to model a malware component after the classic mobile game 'Snake' perfectly encapsulates the bizarre and creative evolution of modern cyber warfare, where nostalgia and espionage unexpectedly intersect. This is not merely a gimmick; it is a clear signal of
The delayed and frantic allocation of resources following a security breach represents a common, yet entirely avoidable, organizational failure that transforms a preventable risk into a catastrophic financial event. As businesses increasingly entrust their most sensitive operations to

A company's digital defenses are often only as strong as its least secure partner, a silent vulnerability that is rapidly becoming the most exploited entry point for cybercriminals across the UK. As businesses grow more interconnected, their supply chains transform into a complex web of