The patch finished without errors, the dashboard glowed green, and yet the quiet question lingered: would you bet the perimeter on that update alone when a state-backed backdoor learned to outlive it? Hours after some networks declared victory, CISA revised its emergency directive and flipped the playbook: patching, once the finish line, became only the starting gun.
Security teams had thought firmware updates closed the book on intrusion risk for Cisco ASA/FTD and Secure Firewall platforms. However, investigators traced persistent command-and-control traffic on “fully updated” devices and tied it to Firestarter, a stealth implant stalking the very web-facing gateways meant to protect the enterprise. The discovery forced a hard pivot from confidence in version numbers to proof of eradication.
Why This Story Matters
Firestarter was linked to UAT-4356, the China-aligned operator behind the ArcaneDoor campaign, which targeted at least one U.S. federal agency. That attribution is not an academic footnote; it signals resources, patience, and repeated zero-day access against high-value edge appliances that are always on and rarely examined deeply.
CISA’s updated Emergency Directive 25-03 reframed the response. The agency stated plainly that “patching does not remove Firestarter if compromise preceded the update,” and required agencies to upload device core dumps to the Malware Next Gen portal, notify CISA on positive findings, and hard-reset impacted devices. Those steps applied across Cisco’s Firepower 1000/2100/4100/9300 and Secure Firewall 200/1200/3100/4200/6100 lines, with verification due by April 24 and hard resets by April 30.
Inside the Backdoor
Researchers found that Firestarter hooked into Lina, Cisco’s core network and security engine, giving the actor arbitrary shellcode execution and a platform for follow-on payloads such as Line Viper. That approach delivered durable, low-noise control with minimal artifacts, aligning with state actor priorities to maintain stealth on perimeter gear. Moreover, it explained why familiar cleanup routines failed to flip the right switches.
The implant also manipulated the Cisco Service Platform mount list so its code ran at boot. Afterward, it restored the list to cover tracks, thwarting routine inspections that compare configuration snapshots. Crucially, the malware could persist through firmware updates when the device never truly lost power. Investigators confirmed that a genuine hard reboot—the physical power pull—severed the foothold and prevented the implant from reappearing.
The Pivot in Guidance
The campaign’s arc featured recurring zero-days. Initial exploitation in 2024 was followed by fresh 2025 bugs, including CVE-2025-20333 and CVE-2025-20362, again abusing the VPN web server path. Even after remediation attempts, operational telemetry showed Firestarter remained active past September 25, underscoring that version upgrades alone did not neutralize the threat.
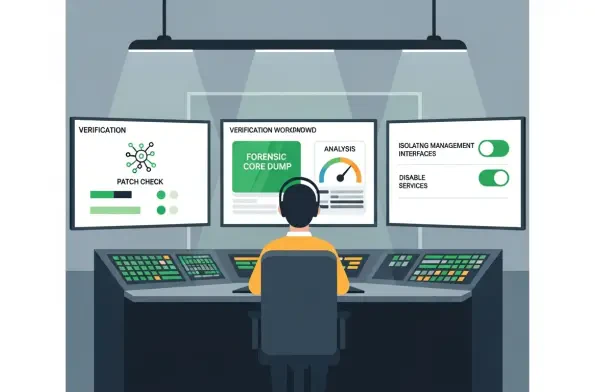
Cisco advisories acknowledged ongoing exploitation and aligned with CISA’s verification-first stance. The directive required agencies to apply the latest patches, isolate management interfaces, and disable nonessential services—then prove cleanliness through core dump analysis. In other words, assurance came from evidence, not from the comforting optics of a green dashboard.
Response Strategy
On the ground, teams stabilized by standardizing updates across in-scope platforms, narrowing admin access, and tightening remote management paths. They generated and uploaded core dumps, triaged results, and coordinated notifications where compromise appeared likely. The process converted uncertainty into a measurable state: either the device still bore traces of Firestarter, or it did not.
Eradication hinged on the unglamorous but decisive step of power cycling. Organizations performed true hard reboots and rebuilt configurations from known-good sources rather than restoring unvetted backups. Afterward, defenders layered monitoring for Lina hooking behaviors, abnormal Service Platform mount changes, and VPN web server anomalies—shifting from passive trust to active verification at the edge.
What to Do Now
The lesson was unambiguous: patching addressed reentry, but only validation and power removal addressed persistence. Agencies that mapped internal deadlines to CISA’s schedule, pre-approved maintenance windows for power cycles, and rehearsed communications with incident response, legal, and executive stakeholders moved from reactive cleanup to disciplined containment.
Looking ahead, the durable playbook rested on cadence. Security teams that added a recurring “edge-appliance compromise assessment” after each patch cycle, treated core dump uploads as standard hygiene, and tuned detections for Lina and mount-list tampering reduced dwell time sharply. The path forward relied on a simple truth that had been proven in practice: resilience emerged when updates, verification, and hard resets worked together, not when patches stood alone.