
Jason Costain
Data Protection SpecialistJason Costain is a security expert specializing in personal data protection. He offers rich insights into incident response planning, cloud security best practices, and the importance of multifactor authentication. With his highly applicable and easy-to-understand publications, Jason empowers his readers with the best methods to protect their sensitive data.
The digital privacy landscape experienced a significant shift recently when it was revealed that forensic investigators could bypass secure messaging encryption by accessing residual data stored within the core operating system of modern mobile devices. This vulnerability, specifically affecting

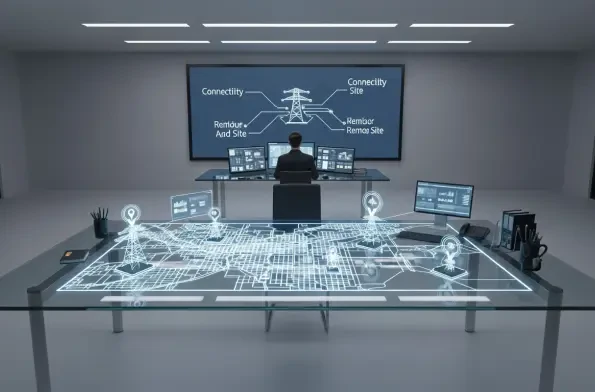
Modern security for critical infrastructure involves much more than simply bolting a gate shut; it requires a digital consciousness that monitors every entry point across vast geographical distances. As industrial landscapes expand, the reliance on mechanical keys has become a liability rather than
The morning ritual of patting pockets for a plastic rectangle or scrolling through digital wallets to find a QR code is rapidly fading into the obscurity of technological history. Every day, more than 131 million Americans perform a silent and subconscious ritual: they glance at their smartphones

While major defense primes like Raytheon and Northrop Grumman have successfully hardened their digital perimeters through massive investments, the smaller entities that make up eighty percent of the Defense Industrial Base remain highly susceptible to sophisticated intrusion. These boutique

Malik Haidar is a cybersecurity expert with extensive experience in combating threats and hackers within multinational corporations. His expertise encompasses analytics, intelligence, and security, with a strong focus on integrating business perspectives into cybersecurity strategies. In this

Defining the New Frontier of Silicon Valley and National Defense The integration of generative artificial intelligence into the most restricted corridors of the United States Department of Defense signifies a fundamental transformation in how global powers prepare for and execute modern warfare.
Developers often assume that package managers are passive conduits for code, yet a single malicious configuration file can turn these essential tools into gateways for total system compromise. The recent release of critical security updates for Composer addressed two high-severity command injection

Our Picks
