Network Security
The forthcoming Linux 6.19 kernel is set to introduce a landmark security enhancement that addresses a long-standing and often overlooked vulnerability at the very heart of modern computing: the unencrypted flow of data across internal hardware buses. For decades, the high-speed PCI Express (PCIe)
As of late 2025, the grace period for compliance has conclusively ended, making the European Union's Network and Information Security 2 (NIS2) Directive an enforced reality for businesses across the continent and beyond. This landmark regulation, which officially replaced its 2016 predecessor

As decentralized networks grapple with the monumental challenge of securely onboarding millions of users, the bottleneck of identity verification has become a primary obstacle to growth and mainstream adoption. Addressing this critical juncture, the Pi Network has initiated a significant strategic

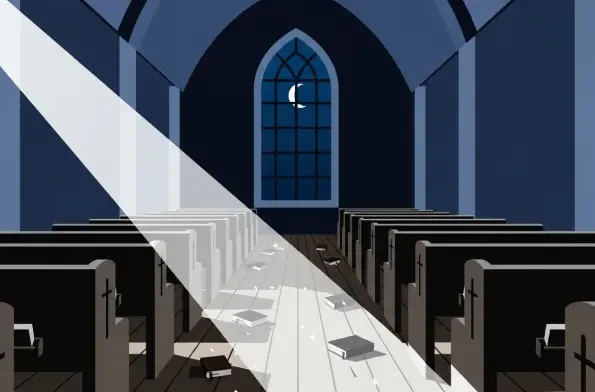
In the wake of a brazen abduction that saw numerous worshippers seized from a Cherubim and Seraphim Church during a sacred night service in Kogi State, Governor Ahmed Usman Ododo is now facing an intense and growing storm of public pressure. Community figures and religious leaders have issued
In a digital landscape where server vulnerabilities can ripple across millions of systems in mere hours, a newly identified flaw known as React2Shell has emerged as a chilling wake-up call for cybersecurity professionals worldwide. Tracked as CVE-2025-55182 with a perfect CVSS score of 10.0, this

Imagine a world where a split-second delay in a game could cost a player victory, or a sudden cyberattack could wipe out hours of progress in an instant. This is the high-stakes reality of modern gaming, an industry that has become a powerful force driving innovation in network technology. With














