Cyber Defense Strategies
The dramatic escalation in the number of security vulnerabilities identified within the Google Chrome ecosystem signals a fundamental transformation in how large-scale software projects are now being defended against sophisticated cyber threats. For several years, security advisories typically

The sudden discovery of a "highly critical" vulnerability within the Drupal content management system has sent ripples through the cybersecurity community, marking a significant departure from the platform's recent period of relative stability. This security flaw, officially tracked

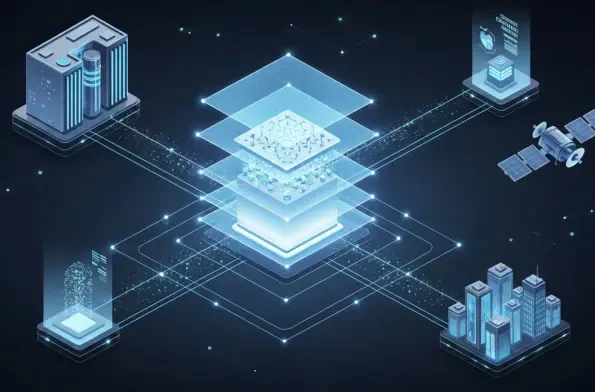
The Crisis: Velocity Without Visibility The global digital ecosystem currently faces an unprecedented paradox where the rapid acceleration of software production has directly compromised the structural integrity of the very systems designed to protect enterprise data. The core of the current
Malik Haidar is a seasoned cybersecurity expert who has spent years at the intersection of threat intelligence and corporate strategy. With a deep background in securing multinational infrastructures, he specializes in bridging the gap between high-level business goals and the technical rigors of

Navigating the internet in 2026 requires a level of vigilance that was once reserved for high-stakes corporate espionage or sensitive political activism. As digital footprints are more aggressively harvested and monetized by global advertising conglomerates and state actors alike, the average

The long-standing reign of stolen passwords as the preferred skeleton key for digital intruders has finally crumbled under the weight of a new, more sophisticated method of entry that targets the very architecture of modern software. For nearly twenty years, the hierarchy of cybercrime remained