Cyber Defense Strategies
A comprehensive journalistic investigation conducted in Austria has brought to light a sophisticated, multi-country disinformation campaign orchestrated by a pro-Russian agent network with direct ties to Russia's Federal Security Service (FSB). This clandestine operation was meticulously

In an industry continuously seeking more accurate and reliable threat detection, the recent strategic acquisition of German 3D LiDAR developer Blickfeld GmbH by Senstar Technologies marks a pivotal moment for the evolution of intelligent security solutions. The definitive agreement, valued at €10.4

The modern smartphone has evolved into an indispensable extension of our digital lives, holding everything from personal memories and financial data to professional correspondence, making the prospect of losing access to it a uniquely distressing event. In this highly connected landscape, a new and
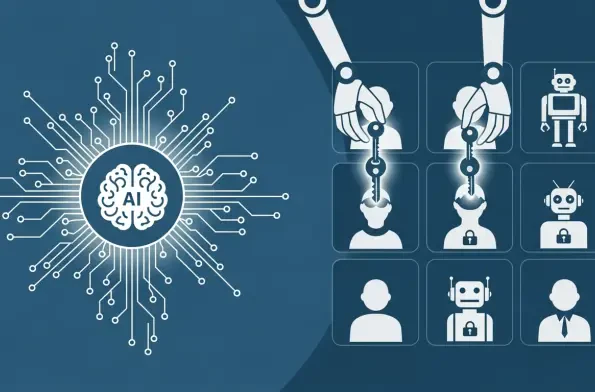
The year 2025 will be remembered as the moment cybersecurity crossed an irreversible threshold, a point of no return where the integration of Artificial Intelligence into the fabric of digital conflict became absolute. This pivotal period marks a distinct "before-and-after" in the

AI-Driven Identity Security is no longer a futuristic concept but a present-day necessity, representing a pivotal advancement in how enterprises protect their most critical assets. This review explores the evolution of this technology, dissects its core features and performance capabilities, and
In an era where centralized IT management tools have become the central nervous system for countless organizations, a single critical vulnerability can trigger a systemic failure with catastrophic consequences. Ivanti's Endpoint Manager (EPM) stands as a testament to this reality, providing