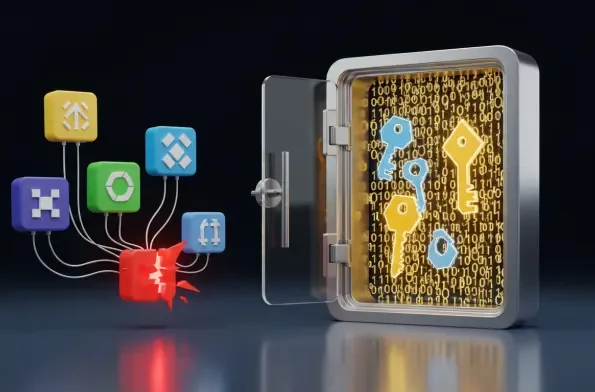
A single innocent-looking theme or productivity add-on can silently compromise an entire development workflow by harvesting high-value credentials without a single permission prompt appearing on the screen. The discovery of a high-severity security vulnerability in Cursor, a popular AI-integrated development environment, has sent ripples through the software engineering community after research revealed a flaw with a CVSS score of 8.2. This vulnerability allows any installed extension to bypass traditional security barriers and exfiltrate sensitive session tokens and API keys. Developers often rely on these tools to accelerate their coding speed, yet the very extensions designed to provide efficiency are now being scrutinized as potential vectors for corporate espionage and data theft. Because the platform does not require specific user interactions to grant database access, the risks extend far beyond simple credential loss to include the potential exposure of private prompts and proprietary metadata that define a company’s unique intellectual property. Furthermore, the lack of transparency in how third-party plugins interact with local resources means that even seasoned professionals might inadvertently invite malicious actors into their most sensitive environments. This situation underscores a growing tension between the rapid adoption of AI-enhanced tools and the foundational principles of secure software architecture. While the convenience of these tools is undeniable, the hidden costs associated with unauthorized service usage and financial liabilities are becoming increasingly difficult for modern enterprises to ignore.
Structural Vulnerabilities in Extensible Development Environments
The fundamental issue stems from a departure from standard security practices, specifically regarding how Cursor manages the storage of sensitive authentication data on the host machine. Instead of leveraging robust operating system keychains, which are specifically designed to encrypt and isolate secrets from unauthorized processes, the platform utilizes a local SQLite database that lacks sufficient protection. This design choice creates a significant security vacuum where any extension, regardless of its stated purpose, can directly query the database to retrieve API keys for services like OpenAI, Anthropic, and Google. Without a permission-based isolation layer, the “secure-by-design” philosophy is effectively abandoned in favor of a more open, yet more vulnerable, architectural framework. This lack of sandboxing means that a simple aesthetic modification or a minor utility tool possesses the same level of data access as the core application itself. Consequently, malicious actors can program extensions to scan for these databases and silently transmit their contents to remote command-and-control servers, leaving almost no trace of the theft. This method of attack is particularly insidious because it bypasses traditional antivirus software that might not flag a legitimate development tool’s database query as a malicious event. Building on this foundation of insecure storage, the incident highlights a broader trend where the race to integrate artificial intelligence often outpaces the implementation of rigorous security controls.
Strategic Mitigation and Evolving Security Standards
Addressing this systematic failure required a fundamental shift in how developers approached the trust boundaries within their integrated development environments during the first half of 2026. While the platform management suggested that the burden of extension vetting rested primarily with the end-user, the industry moved toward more automated verification methods to mitigate these risks. Security teams began implementing strict allow-lists for extensions and utilized network monitoring tools to detect unusual outbound traffic originating from development applications. It became clear that relying on manual inspection was insufficient when extensions could be updated with malicious payloads after their initial installation. Organizations also transitioned toward short-lived session tokens and environment variables rather than persisting long-term API keys within local databases. This shift emphasized that protecting the development lifecycle was as critical as securing the production environment itself. By prioritizing local storage encryption and demanding better process isolation from software providers, the community established a more resilient defense against silent exfiltration. These proactive measures were complemented by a new standard of “least privilege” for local plugins, ensuring that a theme could never access the network or local databases. Moving forward, the industry adopted more transparent auditing tools that allowed developers to visualize exactly what data their extensions were accessing in real-time.