Malik Haidar stands at the intersection of complex network infrastructure and high-stakes cybersecurity, bringing years of experience from the front lines of multinational corporate defense. His work focuses on the philosophy that security is not just a collection of hardware, but a living ecosystem that requires deep integration to remain resilient against modern threats. By bridging the gap between business intelligence and technical analytics, he has helped organizations transform their security posture from reactive firefighting to a streamlined, proactive strategy. In this discussion, we explore the evolving landscape of physical security, focusing on how the convergence of switch diagnostics and site management platforms is redefining operational efficiency and infrastructure resilience for high-security environments.
The conversation covers the transition from fragmented software ecosystems to unified management interfaces, the financial and safety benefits of remote hardware maintenance, and the empowerment of general operational staff through automated diagnostics. We also delve into the prioritization of real-time cyber alerts and the critical role that collaboration between specialized manufacturers plays in closing the security gaps found in government and critical infrastructure sites.
Traditional network management often requires toggling between various software platforms to identify hardware issues. How does unifying switch diagnostics and access control into a single interface change daily operations for security teams, and what specific step-by-step efficiencies are gained during a critical system failure?
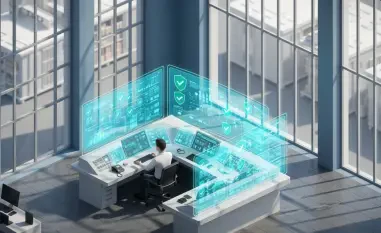
The shift to a single interface like the Command Centre is a game-changer because it removes the cognitive load and “tab fatigue” that plague operators during high-pressure situations. In a traditional setup, when a camera or a reader goes down, the operator has to log into a separate network management tool, hunt for the specific switch, and try to correlate port data with physical locations. With deep-level integration into the Layer 3 managed switch range, that entire diagnostic chain is compressed into a few clicks on one screen. When a critical failure occurs, the system provides an immediate network topology visualization, allowing the team to see the exact point of failure within the infrastructure. This means they can instantly identify if the problem is a faulty cable, a power surge, or a crashed device without ever leaving their primary monitoring seat.
Field maintenance often incurs high costs and safety risks when engineers must travel to physical sites for simple hardware resets. Can you explain how remote port rebooting and network topology visualization impact operational budgets, and what metrics usually demonstrate the shift from reactive to proactive maintenance?
Sending a technician to a remote site or a restricted government area isn’t just expensive; it’s a logistical and safety headache that can cost thousands in billable hours and fuel. By utilizing remote reboot capabilities for IP devices and switch ports directly from the management platform, we can resolve what used to be a four-hour site visit in under sixty seconds. The network topology visualization provides a clear, real-time map that shows exactly how devices are connected, which allows us to spot deteriorating link qualities before they result in a total outage. We typically measure this shift through the reduction in “truck rolls” and a significant increase in system uptime percentages. When you can fix a port at 2:00 AM from a central office rather than dispatching a team to a hazardous or distant location, the impact on the operational budget is immediate and massive.
High-security environments typically require specialized network engineers for routine troubleshooting. How does automating device discovery and SNMP trap alerts allow general operational staff to handle complex diagnostics, and what anecdotes illustrate the transition in skill requirements for these security teams?
The beauty of this integration is that it democratizes complex network data, making it accessible to the people who are actually watching the screens every day. Through automatic discovery and configuration prompts, the system identifies any network changes or new devices instantly, so the staff doesn’t have to be experts in command-line interfaces to understand what is happening. SNMP trap alerts translate “network noise” into actionable security and cyber events that appear right alongside standard door alarms. I’ve seen cases where general security guards, who previously wouldn’t know a switch from a server, were able to identify and isolate a malfunctioning port simply by following the visual cues on their dashboard. This transition means that organizations no longer have to wait for a high-salaried network engineer to wake up and log in just to perform basic troubleshooting.
Cyber threats to IP-based security infrastructure are becoming increasingly sophisticated. What specific types of security and cyber alerts are prioritized through real-time monitoring, and how does this immediate visibility prevent broader system breaches while maintaining maximum network uptime?
In an integrated environment, we prioritize alerts that indicate unauthorized access attempts or unusual traffic patterns at the switch level, which are often the first signs of a lateral movement attack. These SNMP trap alerts are fed directly into the management platform, providing a heartbeat of the entire network’s health and security status. When an operator sees an alert for an unauthorized device trying to bridge a port, they can shut that port down remotely and instantly, preventing a localized issue from becoming a full-scale network breach. This proactive monitoring ensures that the network remains “hardened” without requiring constant manual audits. By catching these anomalies in real-time, we maintain maximum uptime because we are resolving threats in their infancy rather than cleaning up after a successful compromise.
Government and high-security sites have unique demands for infrastructure resilience and data integrity. In these environments, how does a collaborative approach between hardware and software manufacturers solve specific network gaps that standalone products generally cannot address?
Standalone products often act like silos, where the hardware knows what is happening at the physical layer but the software has no idea why a data stream has stopped. A collaborative approach, like the one between barox and Gallagher, bridges this gap by embedding sophisticated monitoring tools directly into the switching technology that “talks” to the site management platform. For government clients, this means they get a level of resilience that is tailored to their specific needs, such as ensuring that every aspect of the IP security network is visible and manageable. This cross-company collaboration allows for the development of unique diagnostic tools that would be impossible if both parties were working in isolation. It’s about creating a unified ecosystem where the hardware and software are essentially two sides of the same coin, providing a level of business value and site integrity that “off-the-shelf” components simply cannot match.
What is your forecast for the future of integrated network management in the global security market?
The global security market is moving toward a future where “dumb” hardware will no longer be tolerated, and every component of a network will be expected to provide deep, actionable intelligence. I predict that the lines between traditional IT networking and physical security will continue to blur until they are indistinguishable, leading to even more automated, self-healing networks. We will see an increased reliance on AI-driven diagnostics that not only alert us to failures but predict them days in advance based on subtle fluctuations in power and data throughput. This evolution will be driven by the need for absolute resilience in the face of both physical and cyber threats, making deep-level integration the standard requirement rather than a premium feature. Ultimately, the winners in this market will be those who prioritize ease of use and total visibility, turning complex infrastructure into a transparent and manageable asset.