Hackers & Threats
Stephen Morai sits down with Malik Haidar, a seasoned cybersecurity leader whose work blends hands-on reverse engineering with business-first risk strategy. With years spent countering sophisticated adversaries in multinational environments, Malik unpacks the rediscovery of fast16—a 2005-era s

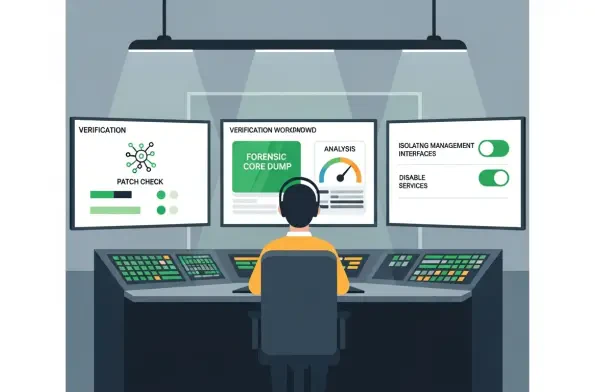
The patch finished without errors, the dashboard glowed green, and yet the quiet question lingered: would you bet the perimeter on that update alone when a state-backed backdoor learned to outlive it? Hours after some networks declared victory, CISA revised its emergency directive and flipped the
The Evolution of Federal Cyber Defense and the Rise of Managed Risk The current security environment represents a complex web where the ghosts of legacy code frequently collide with the rapid-fire innovations of modern cloud infrastructure. As cyber threats transition from opportunistic probes to
The conventional wisdom that digital security begins and ends at the email gateway is rapidly becoming an obsolete relic of a less sophisticated era in cybersecurity history. As organizations have successfully fortified their perimeter defenses against traditional phishing attempts, threat actors

The digital sovereignty of nations is currently being dismantled by invisible actors who exploit the very cloud infrastructures designed to facilitate modern global cooperation and governance. As geopolitical tensions rise, nation-state actors have increased the frequency of intrusions into

The long-standing perception that Apple’s walled garden offers an impenetrable defense against nation-state cyberattacks has finally crumbled under the weight of sophisticated North Korean espionage operations. For years, creative professionals and financial executives operated under the assumption














