
Janine Saintos
Business AdvisorJanine Saintos’ portfolio of work in security, as well as her unique business perspectives, make her content a favorite of C-suite audiences. By combining her knowledge of business and security, Janine helps leaders develop an understanding of a wide range of related topics. Building cyber-resilient organizations, developing business continuity and disaster recovery plans, and cybersecurity due diligence for mergers and acquisitions are some of the themes addressed in her publications.
The delicate architecture of a nation’s prosperity rests upon the unseen digital threads that connect its power grids, financial markets, and communication channels to the wider world. New Zealand currently finds itself at a pivotal crossroads as the government moves to modernize its approach to n

Security professionals frequently encounter a daunting backlog of vulnerabilities, yet the numerical values assigned to these flaws rarely tell the whole story of an impending breach. For decades, the Common Vulnerability Scoring System (CVSS) has functioned as the primary language for

The relentless pace of digital transformation has officially entered a new chapter where security administrators must now contend with vulnerabilities unearthed by machine intelligence rather than human intuition. This month, Microsoft released a security cycle that addresses 83 distinct flaws,

Malik Haidar is a seasoned cybersecurity expert who has spent years bridging the gap between deep technical defense and high-level corporate strategy. Having managed complex security landscapes for multinational corporations, he specializes in transforming raw threat intelligence and operational
The modern medical facility is no longer just a sanctuary for physical healing; it has become a complex digital fortress where a single software glitch can be as life-threatening as a structural failure. To address this precarious reality, the Administration for Strategic Preparedness and Response
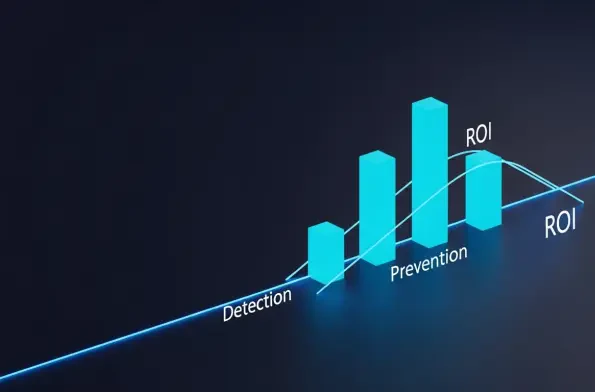
The reality of the modern digital landscape is that eight out of every ten British businesses have faced a serious cyber incident within the last twelve months, creating a climate where passive defense is no longer a viable corporate strategy. As the UK government pushes for a more resilient

The rapid convergence of sophisticated machine learning models and state-level offensive operations has fundamentally altered the digital battlefield by turning theoretical vulnerabilities into functional weapons. This transition marks a departure from the era where artificial intelligence was

Our Picks
