
Janine Saintos
Business AdvisorJanine Saintos’ portfolio of work in security, as well as her unique business perspectives, make her content a favorite of C-suite audiences. By combining her knowledge of business and security, Janine helps leaders develop an understanding of a wide range of related topics. Building cyber-resilient organizations, developing business continuity and disaster recovery plans, and cybersecurity due diligence for mergers and acquisitions are some of the themes addressed in her publications.
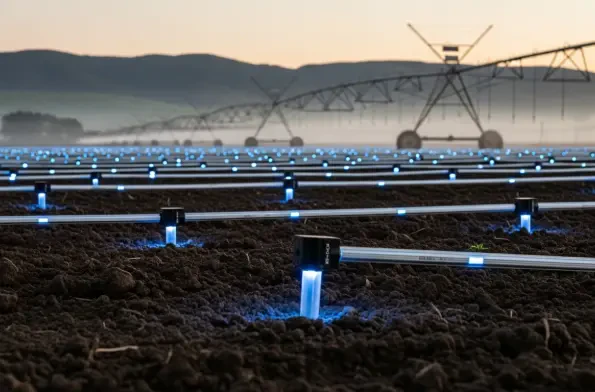
Heavy industries are currently witnessing a seismic shift as they attempt to connect millions of disparate sensors across some of the most inhospitable and geographically isolated regions on the planet, creating a demand for infrastructure that moves beyond the limitations of traditional cellular
The digital landscape has transformed into a high-stakes battlefield where the distinction between a resilient enterprise and a compromised one often depends on the underlying security architecture. As we navigate the complexities of 2026, the industry remains fixated on two undisputed titans:

The traditional belief that a massive cybersecurity budget translates directly into an impenetrable digital fortress is being dismantled by a stark reality: one in five enterprise devices currently operates without functional protection. This massive coverage gap persists despite the fact that
The Cybersecurity and Infrastructure Security Agency has issued an emergency mandate requiring federal civilian departments to immediately address a maximum-severity vulnerability residing within Cisco’s Secure Firewall Management Center. This flaw, tracked as CVE-2026-20131, presents an e

The shifting landscape of modern cybersecurity now dictates that organizations must prioritize identity as the real perimeter rather than relying on legacy firewalls that attackers simply bypass using stolen but valid sign-in credentials. As the industry navigates the complexities of the current

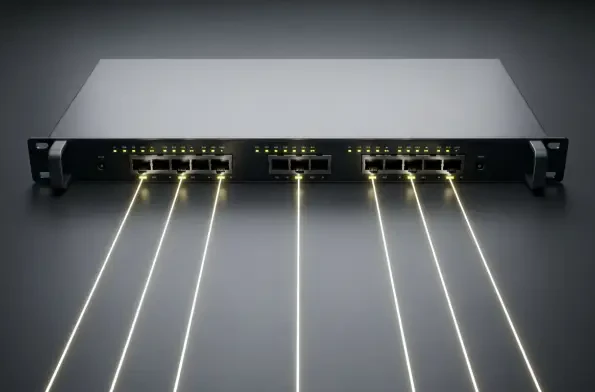
Modern network security is no longer defined solely by the strength of the perimeter but by the resilience of the central orchestration engines that manage global data flows. Recent disclosures regarding the Cisco Catalyst SD-WAN Manager have sent shockwaves through the enterprise sector as threat
Security researchers recently identified a collection of nine cross-tenant vulnerabilities within Google Looker Studio, a discovery that highlights the overlooked risks inherent in business intelligence platforms. These flaws, collectively branded as LeakyLooker, presented a significant threat to

Our Picks
