Security in Digital Transformation
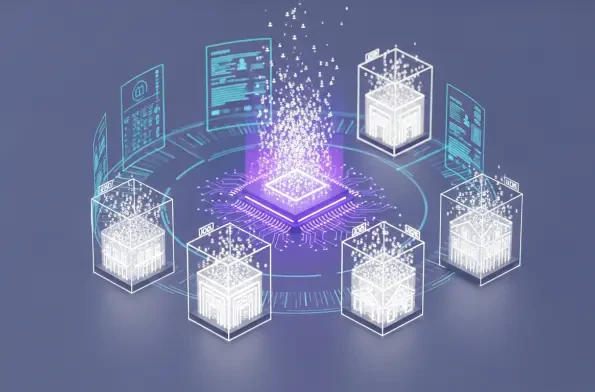
The rapid evolution of autonomous digital agents has forced global financial institutions to move beyond conceptual debates and embrace a new era of engineering rigor. Lloyds Banking Group has taken a definitive stand by treating agentic artificial intelligence not merely as a novelty, but as a

The transition from mechanical brass keys to sophisticated digital ecosystems marks a definitive break from the era when perimeter security was defined solely by the thickness of a steel door. In the current operational climate of 2026, industry reports suggest that over sixty percent of corporate
The landscape of digital security across the British Isles has reached a critical inflection point as organizations find themselves caught in a relentless cycle of sophisticated cyber incursions. While many European neighbors have seen a stabilization in incident frequency, United Kingdom

The long-standing partnership between global software giants and the independent security researchers who find their flaws has reached a volatile breaking point that endangers the safety of every digital user. This delicate truce is currently facing its most severe test as the "social
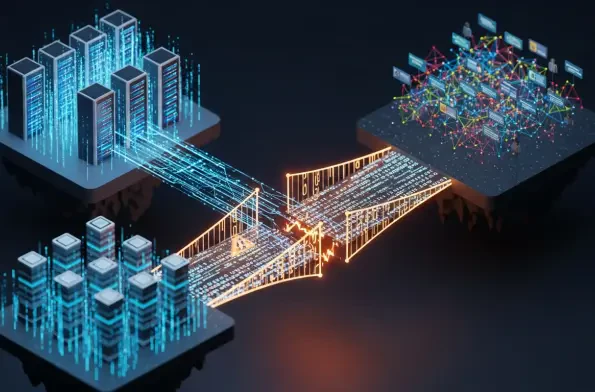
The traditional security perimeter has dissolved as modern enterprises navigate a complex ecosystem where identity, rather than physical office walls, serves as the primary gateway to sensitive digital assets and corporate infrastructure. As organizations continue to grapple with the demands of
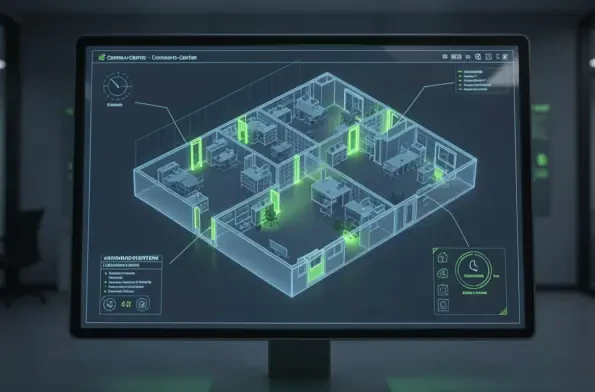
The transition from traditional mechanical locking systems to interconnected digital access solutions has accelerated significantly as urban environments demand more sophisticated security protocols. Organizations no longer view a lock as merely a standalone hardware component but rather as a

1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61













