Network Security
Diving into the world of smart building technology, I'm thrilled to sit down with Malik Haidar, a renowned expert in cybersecurity and building security solutions. With a career dedicated to safeguarding multinational corporations through innovative strategies, Malik brings a unique

Today, we’re diving into the complex world of cyber espionage with Malik Haidar, a seasoned cybersecurity expert with a track record of defending multinational corporations against sophisticated threats. With deep expertise in analytics, intelligence, and security, Malik has a unique perspective on
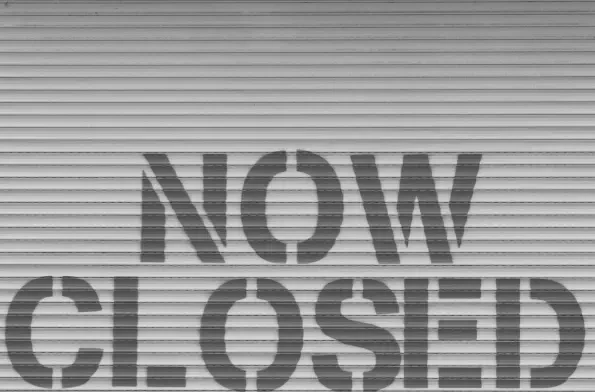
The federal government shutdown that commenced on October 1, 2025, has unleashed a wave of disruption across critical sectors, with the nation’s cybersecurity defenses taking an especially severe hit, particularly at the Cybersecurity and Infrastructure Security Agency (CISA). As the primary c
The digital landscape is buzzing with concern over a critical security flaw in Redis, an in-memory database used by roughly 75% of cloud environments, and this issue has sparked widespread alarm due to its potential impact. Dubbed "RediShell" and identified as CVE-2025-49844, this

In the ever-evolving world of cybersecurity, few names stand out as prominently as Malik Haidar. With years of experience safeguarding multinational corporations from digital threats, Malik has become a leading voice in analytics, intelligence, and security. His unique ability to blend business

What happens when a malicious program can infiltrate the deepest layers of a system, evading even the most advanced security tools, and awaken only at the command of a hidden signal? This isn’t a theoretical nightmare but the stark reality of a sophisticated GNU/Linux rootkit that has emerged as a s