Emerging Threats
The security of a billion-dollar enterprise cloud infrastructure can unexpectedly hinge on the seemingly harmless decision of a single developer to download a gaming automation tool on a personal device. This incident underscores a terrifying reality in modern cybersecurity where the boundary
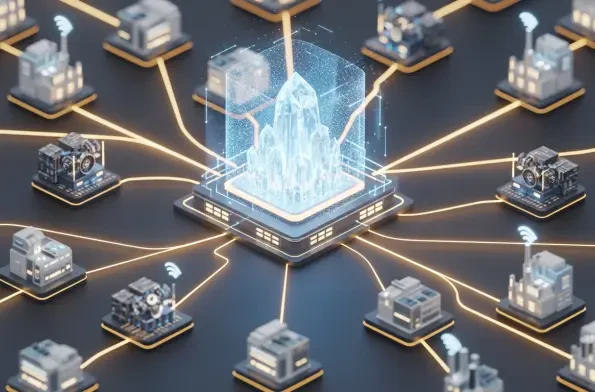
The invisible hardware linking decade-old machinery to high-speed fiber optics has quietly become one of the most significant security bottlenecks in global critical infrastructure today. As organizations across the globe accelerate the integration of operational technology with information

The traditional methodology of manual software development is currently being eclipsed by a sophisticated paradigm where intuition meets machine precision, fundamentally altering how global digital infrastructure is constructed. This evolution, often referred to as vibe coding, signifies a

Digital landscapes in 2026 are increasingly defined by the silent background hum of millions of connected devices, yet this massive expansion of the Internet of Things has simultaneously widened the attack surface for sophisticated threat actors. While modern security protocols have matured
A professional software engineer casually downloads a popular open-source library to streamline a complex project, unaware that a single malicious line in a documentation file is about to compromise their entire local development environment within seconds. This process involves no suspicious
The global automotive sector currently navigates a perilous digital landscape where ransomware has emerged as the most aggressive and disruptive force threatening industrial stability. During the previous year leading into 2026, documented cyberattacks on vehicle manufacturers more than doubled,
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72