Cyber Risk Management
The digital backbone of modern society, encompassing everything from power grids and financial systems to healthcare networks, faces a relentless barrage of sophisticated threats that demand an equally sophisticated defense. In this high-stakes environment, where a single vulnerability can have

In the fast-paced world of digital assets, where immense opportunity is often shadowed by sophisticated security threats, establishing a truly resilient and trustworthy trading environment has become the ultimate priority for leading platforms. Responding to this critical industry need, the

The shuffling of executives in corner offices often goes unnoticed by the public, but a careful examination of recent high-level appointments across the global technology and security landscape reveals a powerful, unspoken consensus on the future of digital defense. These strategic hires are more

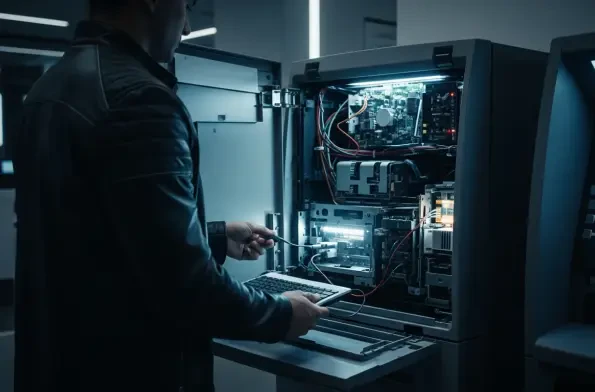
The unassuming cash machine on the corner has become the latest battleground in the fight against international terrorism, as a sophisticated scheme transforms ATMs into unwilling financiers for a designated foreign terrorist organization. The U.S. Department of Justice has unsealed indictments
The seemingly innocent browser extension you installed for a minor convenience could be systematically dismantling your digital security from the inside out, operating silently until its true purpose is revealed. This hidden world of browser-based threats has been brought into sharp focus by a

In the shadowy world of digital finance, a single nation-state has orchestrated a heist so vast and systematic that it now accounts for the majority of all cryptocurrency stolen globally, turning decentralized exchanges into its de facto treasury. This is not the work of disparate criminal gangs














