Cyber Defense Strategies
The lines once drawn by firewalls and network gateways have evaporated, leaving behind a digital landscape where the only constant, the only true defensible border, is the identity of who or what is accessing critical data. The cybersecurity industry has reached an inflection point, a moment

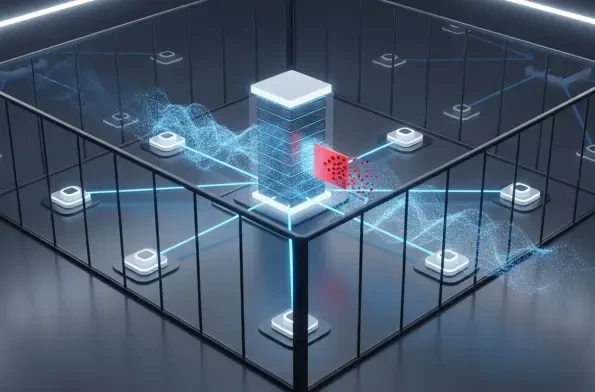
The very systems designed to centralize and enforce an organization's endpoint security can, under specific circumstances, become the most critical point of failure, granting attackers widespread access with a single exploit. Such is the case with a recently disclosed vulnerability in
The very foundation of digital trust that underpins modern business communication is crumbling under the weight of an unprecedented wave of sophisticated, AI-driven cyber attacks that existing defenses were never designed to handle. A staggering 88% of organizations have suffered a security

The very digital fabric connecting Europe's economies, governments, and societies now serves as a primary battleground for sophisticated threat actors, making organizational resilience not just a technical goal but a fundamental imperative for survival. A confluence of geopolitical

Amidst roiling domestic protests that capture global headlines, a parallel, quieter conflict wages on in the digital realm, one where Iran's state-sponsored cyber operatives show no signs of ceasing their espionage activities against a growing list of perceived adversaries. This persistent

The very fortress built to protect our most private conversations is now being turned against us, not with battering rams of code, but with whispers of deception that exploit the one vulnerability no encryption can patch: human trust. As high-value targets, from politicians and military leaders to














