Cyber Defense Strategies
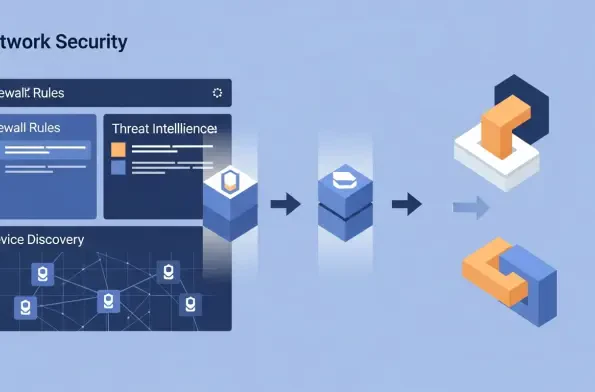
The latest major release of the open-source firewall platform, OPNsense 26.1, codenamed "Witty Woodpecker," marks a significant evolution in network security management by introducing a powerful API-driven architecture and a suite of new tools designed for modern IT environments. This
In the relentlessly evolving landscape of cybersecurity, where threats multiply and solutions vie for attention, the most authentic measure of a platform's value comes directly from the professionals who rely on it daily. It is within this context that CrowdStrike has once again demonstrated

Securing the foundational code that underpins a vast portion of the digital world requires a strategy that is as dynamic and resilient as the software itself. The Linux kernel development community, led by key figures such as Greg Kroah-Hartman, is executing a comprehensive and proactive overhaul
The proliferation of smart home devices has quietly transformed the typical household network into a sprawling, unsecured digital landscape where every connected gadget, from your security camera to your coffee maker, can freely communicate with one another. This "flat" network

The relentless pace of cloud adoption has fundamentally altered the security landscape, rendering traditional vulnerability management practices obsolete and leaving many organizations dangerously exposed. In today's dynamic cloud environments, where infrastructure can be deployed and

While the investment world remains captivated by the explosive growth of artificial intelligence, a parallel and equally critical industry is quietly gearing up for a decade of unprecedented expansion. The same sophisticated AI models that are revolutionizing productivity and creating new markets














