Compliance & Regulations
The rapid evolution of autonomous digital agents has forced global financial institutions to move beyond conceptual debates and embrace a new era of engineering rigor. Lloyds Banking Group has taken a definitive stand by treating agentic artificial intelligence not merely as a novelty, but as a

Security professionals frequently encounter dashboards displaying flawless rows of green checkmarks that provide a false sense of security, yet these pristine records can often conceal significant vulnerabilities lurking beneath the surface of an organization. This phenomenon occurs when compliance

The transition from mechanical brass keys to sophisticated digital ecosystems marks a definitive break from the era when perimeter security was defined solely by the thickness of a steel door. In the current operational climate of 2026, industry reports suggest that over sixty percent of corporate
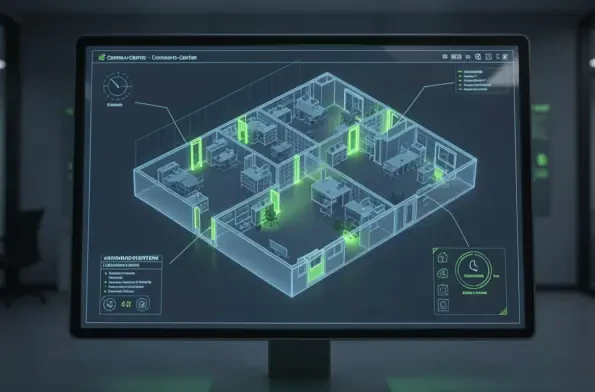
The traditional security perimeter has dissolved as modern enterprises navigate a complex ecosystem where identity, rather than physical office walls, serves as the primary gateway to sensitive digital assets and corporate infrastructure. As organizations continue to grapple with the demands of
The ongoing tension between global technological dominance and national security requirements reached a critical juncture recently as federal regulators intensified their scrutiny of uncrewed aerial systems manufactured abroad. This atmosphere of heightened suspicion placed DJI, the world’s leading

The rapid migration of criminal activity to encrypted digital platforms has created a strategic blind spot that threatens the effectiveness of modern law enforcement agencies, necessitating a profound shift in how democratic states manage digital evidence and the legal frameworks that govern it. As

1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56













