AI in Cybersecurity
In an era where digital threats evolve faster than ever, the cybersecurity landscape stands at a pivotal crossroads with artificial intelligence emerging as both a powerful ally and a potential risk. Imagine a world where cyber attackers use AI to craft sophisticated breaches that outpace

Imagine a cybersecurity team drowning under a tidal wave of alerts, each notification screaming for attention while critical threats slip through unnoticed amidst the chaos of irrelevant warnings. This isn’t a far-fetched scenario but a daily reality for countless security professionals grappling w

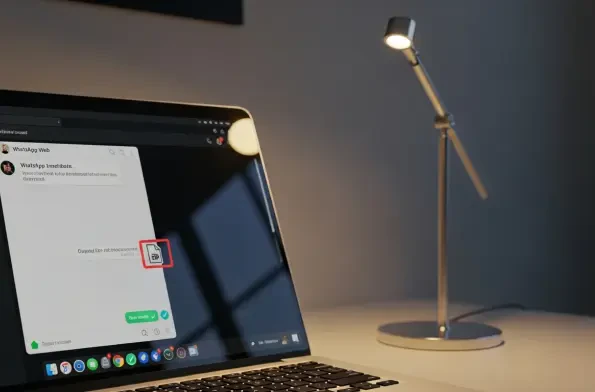
Imagine opening WhatsApp Web to chat with a trusted contact, only to receive a seemingly harmless message with an attachment that, once clicked, unleashes a devastating banking trojan stealing sensitive financial data. This isn’t a far-fetched scenario but the chilling reality of a sophisticated c
In an era where cyber threats loom larger than ever, with data breaches and ransomware attacks costing businesses billions annually, the search for reliable cybersecurity investments feels like striking gold in a volatile market. Fortinet Inc. (ticker: FTNT) emerges as a shining contender, blending

Founders chasing product-market fit increasingly describe features in plain language and watch large language models convert ideas into code, turning pitch decks into running demos before competitors finish staffing sprint zero. This shift, dubbed vibe coding, lowers the bar to build and narrows
In an era where artificial intelligence drives innovation at an unprecedented pace, the dark side of this technological revolution has emerged as a formidable threat, with state-linked actors exploiting AI platforms for malicious purposes. A San Francisco-based startup, Factory, recently found














