The invisible hardware linking decade-old machinery to high-speed fiber optics has quietly become one of the most significant security bottlenecks in global critical infrastructure today. As organizations across the globe accelerate the integration of operational technology with information technology, serial-to-IP converters have emerged as a primary target for sophisticated threat actors. These devices, which serve as the essential translators between legacy serial protocols and modern Ethernet networks, were originally designed for functionality rather than security. This oversight has created a sprawling attack surface where ancient mechanical reliability meets the volatility of the modern internet.
The State of Global Connectivity and Emerging Risks
Market Adoption and the Expansion of the Attack Surface
The rapid convergence of operational and information technology has made serial-to-IP converters indispensable for modernizing legacy equipment in the energy and manufacturing sectors. While these converters allow for remote monitoring and improved efficiency, they also introduce modern vulnerabilities to hardware that was never intended to be network-facing. Recent cybersecurity research, particularly the discovery of the BRIDGE:BREAK vulnerabilities, highlighted the severity of this issue by uncovering 20 critical flaws across leading vendors like Silex and Lantronix. These flaws facilitate unauthorized access, allowing attackers to bypass traditional security perimeters with startling ease.
The scale of this exposure is not merely theoretical but is backed by concrete data from open-source intelligence tools. Utilizing platforms such as Shodan, security analysts identified nearly 20,000 internet-exposed devices that remain vulnerable to remote exploitation. Many of these devices are configured with default credentials or outdated firmware, making them “low-hanging fruit” for automated exploit scripts. The proliferation of these exposed bridges means that a single vulnerability in a common hardware component can have a ripple effect across thousands of distinct industrial networks.
Critical Applications in Modern Infrastructure
In the healthcare sector, these converters facilitate vital communication for life-critical devices, including infusion pumps and laboratory information systems. When a serial-to-IP bridge is compromised in a clinical environment, the consequences extend far beyond data theft. An attacker could potentially disrupt surgical workflows or alter the reporting of patient vitals, leading to life-threatening delays or incorrect treatments. The integration of legacy medical hardware into modern hospital networks has inadvertently placed patient safety at the mercy of decades-old protocol translation.
Industrial Control Systems also rely heavily on serial device servers to monitor manufacturing sensors and maintain power grid stability. Historical case studies, such as the 2015 Ukrainian power grid attack and recent energy sector breaches in Poland, demonstrate that serial-to-IP vulnerabilities are already a part of the modern warfare playbook. By targeting these bridges, state-sponsored actors and cybercriminals can manipulate sensor readings to hide physical damage or trigger emergency shutdowns, proving that the digital-to-physical bridge is a critical point of failure.
Expert Perspectives on Vulnerability Management
Cybersecurity researchers have voiced growing concern over the prevalence of unauthenticated remote code execution and firmware tampering in these legacy bridges. Because these devices often sit in the background of a network, they are frequently excluded from standard IT patching cycles. This “set it and forget it” mentality has allowed critical vulnerabilities to persist for years. Experts argue that until these components are treated with the same rigor as servers or workstations, they will continue to serve as a gateway for lateral movement within sensitive networks.
Analysis of recent advisories from the Cybersecurity and Infrastructure Security Agency suggests a shift in how the government views these “overlooked” hardware components. There is a growing industry consensus that the hardware used in critical infrastructure must adhere to “secure-by-design” principles. This movement pushes manufacturers to disable insecure services by default and implement cryptographically signed firmware updates. However, the challenge remains in retrofitting these standards onto millions of devices already deployed in the field.
The Evolution of OT Security and Future Projections
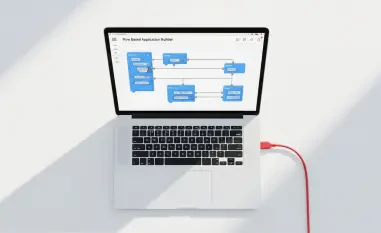
The industry is currently transitioning from simple network translation toward the use of intelligent, encrypted edge gateways. These next-generation devices offer built-in firewalls and deep packet inspection, providing a layer of security that simple converters lack. Despite this technological progress, the persistence of legacy hardware cycles remains a major hurdle. Many industrial sites operate on ten-to-fifteen-year replacement schedules, meaning that vulnerable hardware will likely remain in operation for the foreseeable future, necessitating more creative defensive strategies.
The move toward strict network segmentation and zero-trust architectures has become the gold standard for defending against compromised converters. By isolating these devices in restricted zones and requiring strict authentication for any data flow, organizations can prevent a compromised bridge from becoming a launchpad for a full-scale network breach. The future of industrial security depends on the ability to wrap these legacy components in modern defensive “cocoons” that mitigate their inherent weaknesses while preserving their operational utility.
Strategic Conclusion: A Path Forward
The analysis of serial-to-IP converter security demonstrated that the bridge between legacy reliability and modern connectivity was a significant vulnerability in the global infrastructure. Organizations that prioritized immediate action, such as implementing firmware updates and robust network segmentation, successfully mitigated the highest risks. It was recognized that the “overlooked” nature of these hardware components required a fundamental shift in asset management and visibility. The move toward zero-trust architectures proved essential in preventing lateral movement from compromised devices. Ultimately, the industry learned that securing the link to the past was a prerequisite for a safe and connected future.