Security
The digital extortion that once locked personal photos for a few hundred dollars has metastasized into a sophisticated criminal enterprise capable of bringing global supply chains to a standstill, demanding multi-million-dollar payments from the world’s largest corporations. This dramatic t

With the European Union's NIS2 Directive now in full force, the lines between physical and cybersecurity have irrevocably blurred, creating a new and challenging compliance landscape. For organizations managing critical infrastructure, the stakes have never been higher, with fines for

The prevailing belief that cybercriminals only hunt for large, high-profile corporations is not just outdated; it is a direct threat to the survival of small and medium-sized businesses everywhere. This dangerous assumption fosters a false sense of security, leaving the digital doors of smaller

The integrity of the justice system is often measured by what happens outside of prison walls, yet it is fundamentally guaranteed by the concrete, steel, and advanced systems meticulously engineered within them. While philosophies on rehabilitation and management evolve, the tangible infrastructure

The long-standing reliance on physical keys and plastic cards for securing our spaces is rapidly giving way to a more integrated, intelligent, and fluid approach centered on the one device nearly everyone carries. Mobile-Based Access Control represents a significant advancement in the security and

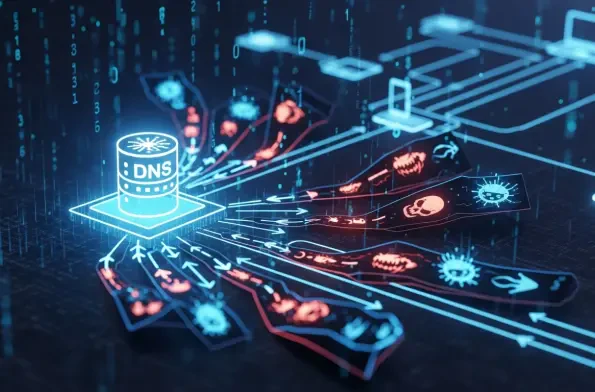
A protocol foundational to the entire internet's operation is now being systematically weaponized to deliver malware in a way that bypasses conventional security, turning everyday network chatter into a Trojan horse. Recent threat intelligence has brought to light a sophisticated evolution of