Security
The line between a trusted colleague on a video call and a state-sponsored actor intent on draining corporate accounts has become dangerously blurred, creating a new paradigm of digital impersonation that challenges the very foundation of online trust. This report analyzes a sophisticated

Today, we're speaking with Malik Haidar, a cybersecurity expert with deep experience tracking and dismantling threats within major corporations. We're delving into a recent incident involving a sophisticated Chinese-nexus threat cluster, a critical zero-day vulnerability in a widely used

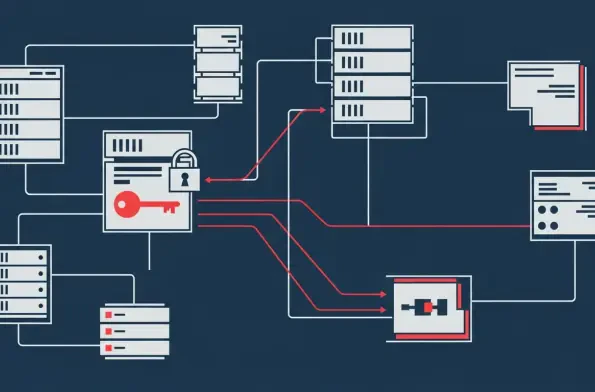
Vast troves of today's most sensitive encrypted data are being systematically stolen and stockpiled, not for immediate use, but to be unlocked by a key that does not yet exist. This strategy, known as "harvest now, decrypt later," represents a paradigm shift in data security, where

With a career built on defending multinational corporations from the digital frontlines, cybersecurity strategist Malik Haidar has a unique perspective on the convergence of physical and digital threats. He joins us to dissect the evolution of a decade-long partnership between Gallagher Security

A new digital battleground is emerging where well-intentioned legislative efforts to protect children online are colliding with the fundamental rights to privacy and free expression. This analysis examines the growing trend of governments proposing restrictions on Virtual Private Networks (VPNs),

The digital ramparts protecting a nation's most sensitive information are not built of stone but of code, policy, and human vigilance, a reality that places Australia at a critical juncture in its ongoing cyber security campaign. Recent comprehensive assessments of the Commonwealth's