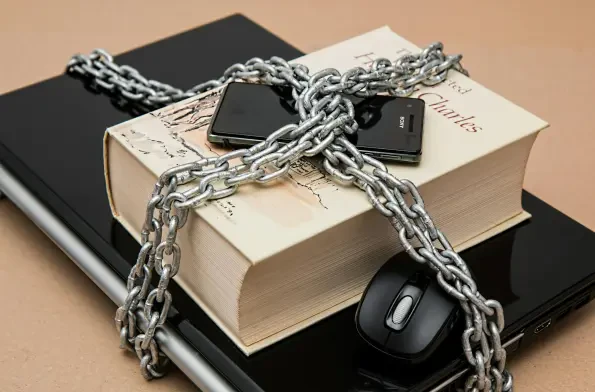
Security
In an era where digital threats evolve at breakneck speed, a staggering reality emerges: cybercriminal groups are no longer just hacking for data—they’re building business models around extortion. Among these, Scattered Lapsus$ Hunters, a faction tied to the sprawling network known as "The Com
In an era where cybersecurity threats loom larger than ever, the discovery of severe vulnerabilities in widely used networking equipment has sent shockwaves through the tech community, raising urgent questions about the safety of business and personal data. Researchers at Forescout’s Vedere Labs h

In an era where digital connectivity underpins nearly every facet of industrial operations across the European Union, a staggering statistic emerges: nearly one-fifth of cyber threats now target operational technology (OT) systems, critical for managing industrial control systems and

Diving into the world of smart building technology, I'm thrilled to sit down with Malik Haidar, a renowned expert in cybersecurity and building security solutions. With a career dedicated to safeguarding multinational corporations through innovative strategies, Malik brings a unique

In today’s hyper-connected digital environment, where cyber threats lurk around every virtual corner, the tools designed to shield systems from harm can sometimes become the very targets of sophisticated attacks. Recently, two medium-severity vulnerabilities have come to light in CrowdStrike’s Fal

The digital landscape is buzzing with concern over a critical security flaw in Redis, an in-memory database used by roughly 75% of cloud environments, and this issue has sparked widespread alarm due to its potential impact. Dubbed "RediShell" and identified as CVE-2025-49844, this














