Security
Today, we’re sitting down with Malik Haidar, a renowned cybersecurity expert who has spent years safeguarding multinational corporations from digital threats and hackers. With a deep background in analytics, intelligence, and security, Malik brings a unique perspective by blending business strategy
In a world where security threats evolve at an alarming pace, consider a sprawling university campus facing a sudden emergency—a potential intruder alert with mere minutes to respond, and security teams needing to sift through hours of footage from dozens of cameras to identify the threat in real t
In today’s fast-paced corporate world, imagine stepping up to an office door, turnstile, or elevator with nothing but a smartphone or smartwatch in hand—and gaining entry with a simple tap. This seamless experience is no longer a distant dream for employees at BNY, a global financial giant with a sp

In an era where children are increasingly exposed to the vast and often unregulated expanse of the internet, a pressing question emerges: how can society shield its youngest members from harmful content while preserving the freedoms that define the digital world? A proposed bill in Michigan has

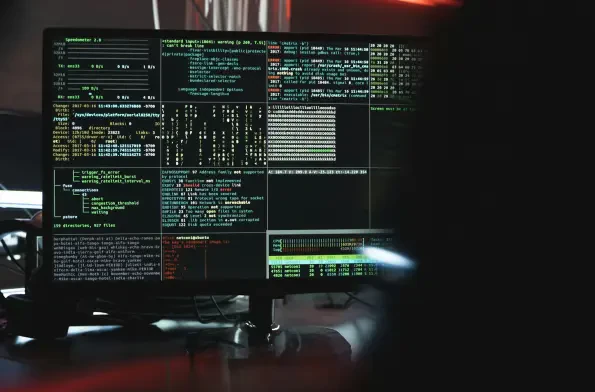
In an era where cyber threats evolve at an alarming pace, keeping abreast of the latest advancements in endpoint security and network monitoring is not just beneficial but essential for safeguarding digital infrastructures. For the week of October 3rd, a wealth of updates from leading industry

In an era where digital connectivity underpins nearly every aspect of business and personal life, the rise of remote work, cloud adoption, and increasingly sophisticated cyber threats has exposed the fragility of traditional network security models. The notion of a secure perimeter, once considered














