The modern digital landscape demands more than just a passive watchful eye; it requires a sophisticated fusion of live intelligence and automated response to stay ahead of increasingly agile adversaries. This paradigm shift marks the end of an era where simply recording events was enough to maintain a perimeter. Today, the focus has moved toward an integrated model where intelligence is not just a secondary data feed but the very engine that drives every security decision. Organizations that fail to bridge the gap between information gathering and active defense often find themselves buried under an avalanche of alerts that lead to analysis paralysis.
Transitioning from Reactive Defense to Strategic Resilience
Traditional security monitoring has long relied on a reactive posture, where teams wait for an alarm to trigger before investigating a potential breach. However, industry experts now suggest that this model is insufficient for organizational survival. The transition to strategic resilience requires a fundamental change in how speed and precision are valued. Speed is no longer just a technical requirement; it is the defining factor in whether an entity can contain a threat before it escalates into a catastrophic failure. Precision, meanwhile, ensures that security resources are not wasted on false positives, allowing the defense to remain lean and effective.
Within this new framework, Mean Time to Repair (MTTR) has evolved from a simple technical metric into a critical indicator of business risk and financial stability. A prolonged MTTR does not merely suggest a slow technical team; it signifies a direct threat to the bottom line, affecting insurance premiums, customer trust, and regulatory compliance. When a threat lingers within a network, the potential for data exfiltration and lateral movement grows exponentially. Consequently, reducing MTTR is now viewed by executive leadership as a vital strategic objective rather than a back-office maintenance task.
Mature security operations distinguish themselves by their ability to collapse information silos that traditionally separate threat intelligence from operational workflows. In less sophisticated environments, intelligence often exists in isolation, requiring manual extraction and correlation during a crisis. High-maturity organizations, by contrast, transform threat intelligence into a decisive operational advantage by ensuring it is available at every stage of the incident lifecycle. This integration allows for a seamless transition from detection to containment, effectively turning abstract data into a shield that protects the organization’s most valuable assets.
The Architecture of a High-Performance Security Operation
Eradicating Operational Friction by Collapsing Information Silos
Slow response times are frequently a symptom of structural failure within fragmented workflows rather than a simple lack of personnel. When an analyst is forced to jump between multiple consoles to verify a single alert, the resulting operational friction creates dangerous delays. These silos prevent a unified view of the threat landscape, leaving individual team members to piece together fragments of an attack without a clear picture of the overall campaign. Structural integration seeks to remove these barriers, ensuring that data flows freely between disparate security tools and teams.
The “context-switching” tax found in legacy Security Operations Centers (SOCs) remains one of the most significant hurdles to efficiency. Every time an analyst leaves their primary dashboard to search an external database, cognitive momentum is lost, and the risk of error increases. In contrast, high-maturity environments leverage seamless data integration to bring all necessary context into a single pane of glass. This approach minimizes the time spent on administrative tasks and maximizes the time spent on high-value analysis, ensuring that the defense remains as fast as the incoming threats.
Addressing the challenge of manual handoffs is essential for creating a high-performance operation. Embedding intelligence at the exact moment of decision-making eliminates the need for an analyst to “go looking” for answers. When a tool automatically enriches an alert with known threat actor profiles or historical data, the decision to escalate or dismiss becomes instantaneous. This reduction in manual labor not only speeds up the response but also reduces the burnout often associated with repetitive, low-context tasks in the SOC.
Shifting Visibility Upstream with Early-Warning Detection Systems
Transitioning from reactive internal telemetry to proactive identification of external command-and-control (C2) infrastructure is a hallmark of an advanced defense strategy. By monitoring the infrastructure that attackers use to orchestrate their campaigns, organizations can identify threats before they ever touch the internal network. This upstream visibility allows security teams to anticipate attacks rather than merely reacting to them. Understanding the “neighborhood” of a potential threat enables the defense to preemptively block suspicious domains and IP addresses that show signs of malicious intent.
The ingestion of real-time indicators of compromise (IOCs) provides the necessary fuel for these early-warning systems. When these indicators are integrated into the detection pipeline, teams can neutralize threats before they have a chance to establish persistence or move laterally. This proactive stance is particularly effective against automated attacks that rely on speed to overwhelm traditional defenses. By matching incoming telemetry against a global database of known threats in real time, the organization can maintain a defensive perimeter that is both broad and deep.
The risk reduction associated with this approach is best described as “removing the fuel” of an attack rather than simply reacting to the fire. If a security team can identify and block the delivery mechanism of a malware strain before it executes, the potential for damage is effectively zeroed out. This shift in focus from remediation to prevention changes the economic calculus for the attacker, making the organization a much harder target. Ultimately, shifting visibility upstream ensures that the security team is always one step ahead of the adversary.
Democratizing Data Through AI-Driven Triage and Natural Language Queries
Artificial intelligence and intuitive search interfaces are revolutionizing how security teams handle massive volumes of data. By empowering junior analysts to perform complex data investigations that were previously reserved for Tier 3 experts, organizations can better utilize their human capital. These tools provide a layer of abstraction that translates complex technical data into understandable insights, allowing for faster and more accurate triage. The result is a more resilient team where knowledge is distributed rather than being concentrated in a few overworked specialists.
The shift away from intricate query syntax toward natural language processing has significantly reduced the “cognitive load” on security staff. Analysts no longer need to spend years mastering specific scripting languages to find the information they need; they can simply ask questions in plain language. This democratization of data access ensures that the focus remains on the investigation itself rather than the mechanics of the tool. It also allows for a more diverse range of professionals to enter the field, helping to close the persistent skills gap in the cybersecurity industry.
There is a growing challenge to the assumption that only veteran experts can handle high-stakes triage. When provided with tools that deliver instant behavioral context and automated risk scoring, less experienced staff can make high-confidence decisions with minimal supervision. This capability is crucial for managing the sheer volume of alerts generated by modern enterprise networks. By providing a clear path from alert to action, AI-driven triage ensures that no critical threat is missed due to human oversight or lack of experience.
Turning Fragmented Logs into Coherent Behavioral Narratives
The evolution of incident response involves moving from “stitching together” disparate logs to leveraging sandbox-derived behavioral intelligence for a full attack chain view. In the past, analysts had to manually correlate timestamps and IP addresses across various systems to understand an attacker’s movements. Today, behavioral narratives provide a pre-constructed story of the attack, showing exactly how a threat entered, what it touched, and where it attempted to go. This holistic view transforms the investigation from a guessing game into a streamlined verification process.
A comparative analysis of Tactics, Techniques, and Procedures (TTPs) allows teams to see the “why” behind an attack rather than just the “what.” Understanding the behavior of a threat actor provides a layer of intelligence that persists even if the specific IOCs, such as file hashes, are changed. This focus on behavioral patterns makes it much harder for attackers to evade detection through simple obfuscation. When an analyst knows the standard operating procedure of a specific threat group, they can anticipate the next move and set traps accordingly.
The future of incident response is one where clarity and “the speed of confidence” replace the ambiguity of raw, uncontextualized data. When the security team has access to a coherent narrative, the time spent on debating the nature of a threat is eliminated. This clarity allows for more aggressive containment strategies, as the risk of accidental disruption to legitimate business processes is minimized. Ultimately, the ability to tell a complete story about an incident ensures that the organization can learn from every encounter and continuously harden its defenses.
Implementation Frameworks for Intelligence-Led Response
The fundamental shift in modern security is the movement from gathering vast quantities of raw data to prioritizing actionable behavioral context. Organizations realized that data without meaning is a liability, creating noise that masks actual threats. By focusing on the behaviors that indicate a breach, security teams streamlined their operations to ignore the irrelevant and focus on the critical. This transition required a disciplined approach to data management, ensuring that every piece of information collected served a specific defensive purpose.
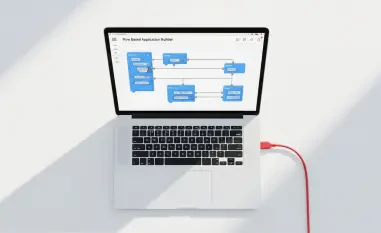
Actionable recommendations for this shift often center on integrating threat intelligence directly into Security Orchestration, Automation, and Response (SOAR) platforms. By feeding high-confidence intelligence into automated playbooks, organizations enabled immediate containment of threats without human intervention. For instance, when a known malicious file hash was detected, the system automatically isolated the affected endpoint and blocked the source IP at the firewall. This level of integration transformed the SOC from a manual review shop into an automated defense engine.
Transitioning a security team from a “firefighting” unit into a proactive threat-hunting organization was achieved through a change in mindset and tooling. Instead of waiting for alerts, teams began to use intelligence reports to look for signs of advanced persistent threats that might have bypassed standard detections. This proactive hunting allowed for the discovery of stealthy intruders before they could achieve their objectives. By dedicating time and resources to hunting, organizations moved beyond simple compliance and into a state of active, continuous defense.
Future-Proofing the Enterprise Through Integrated Resilience
The strategic adoption of integrated intelligence proved to be the primary catalyst for turning a reactive security posture into a streamlined defense machine. Organizations that embraced this model found that they were not only better protected but also more agile in the face of new threats. The maturity of the SOC became a direct reflection of the organization’s ability to withstand and recover from cyberattacks. This resilience was not built overnight but was the result of a consistent commitment to breaking down silos and prioritizing context over raw data.
The strategic importance of a mature SOC was recognized as a key factor in protecting an organization’s long-term reputation and operational continuity. In an environment where a single breach could cause irreversible damage, the ability to respond with speed and precision was invaluable. Security was no longer viewed as a cost center but as a fundamental pillar of business stability. Leaders who understood this were able to secure the necessary investments to keep their defenses ahead of the curve, ensuring that their enterprises remained competitive and secure.
Viewing security efficiency as a strategic business lever rather than a back-office expense allowed organizations to unlock new levels of performance. The focus shifted toward how security could enable the business to take calculated risks by providing a safety net of integrated intelligence. This perspective ensured that security teams were aligned with the broader goals of the organization, moving away from being a “department of no” to a “department of how.” As a result, the enterprise was not only more secure but also better positioned to navigate the complexities of the modern digital economy.