
Marla Pairira
Compliance AdvisorMarla Pairira is a writer interested in hackers and threats. She writes from the perspective of ethical hackers, helping businesses uncover vulnerabilities and comply with regulations like GDPR and HIPAA. Marla also looks at the moral, ethical, and legal issues, advising organizations on responsible disclosure and sharing the guidelines for obtaining proper authorization.
The digital landscape has evolved into a complex and treacherous battlefield where the lines between state-sponsored espionage, organized crime, and opportunistic exploitation have become dangerously blurred. A new paradigm of threat has emerged, one not defined by isolated hackers but by an

The simple, convenient act of tapping a payment card to a smartphone has been ingeniously weaponized by a sophisticated cyber campaign, transforming a feature designed for ease of use into a silent tool for financial theft. A new and highly evasive form of Android malware, dubbed "Ghost

The rapid integration of sophisticated AI into the world's digital town squares has reached a critical inflection point, as a wave of international regulatory actions now targets X and its generative AI, Grok, over the proliferation of synthetic pornographic content. This is not just another
Introduction The sponsored links at the top of a search engine results page often seem like a shortcut to a trusted destination, but a recent international operation reveals they can also be the gateway to devastating financial fraud. The takedown of a sophisticated phishing website by the U.S.

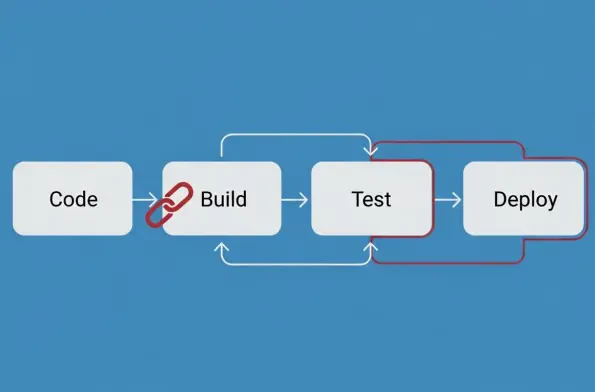
A recent, extensive analysis of software supply chains has brought to light a dangerously sophisticated and escalating threat targeting developers through widely trusted open-source repositories. This investigation uncovered two distinct but thematically linked campaigns that underscore a troubling

The year 2025 will be remembered in cybersecurity circles not just for the record-breaking volume of new vulnerabilities disclosed but for the strategic precision with which threat actors exploited them to undermine the global software supply chain. An unprecedented surge in Common Vulnerabilities
The unassuming smart TV in the corner of the living room, once a symbol of modern convenience, has quietly become a soldier in a colossal cyber army, following the discovery of the Kimwolf botnet. This sprawling network, comprising an estimated 1.8 million devices, signals a new era in cyber

Our Picks
