
Kristen Papadaikis
Security AdvisorKristen Papadaikis lends her expertise on business perspectives to security specialists. She offers tangible advice on maintaining robust security measures for businesses operating with remote or hybrid workforces, which has proven essential for staying ahead in a post-pandemic environment. Kristen’s work has been instrumental in helping companies stay ahead of security threats as the business landscape changes.
As industrial sectors like manufacturing, energy, and transportation increasingly connect their operations to the internet, they expose once-isolated critical infrastructure to a new and dangerous breed of sophisticated cyber threats. Traditional security measures, long focused on building static

The very tools millions of users trust to shield their online activities from prying eyes may be the ones actively betraying their confidence, creating a digital paradox where privacy becomes the price of admission. A startling investigation has brought to light serious allegations against Urban

The High-Stakes Gamble on a Connected World's Security Every smart thermostat, connected car, and automated factory floor represents a potential entry point for cyber threats, a vulnerability that one company believes it can seal with a massive new influx of capital. The Internet of Things

A New Era of Defense Cybersecurity: ISACA Takes the Helm In a landmark decision set to redefine cybersecurity validation across the global defense landscape, the U.S. Department of Defense (DoD) has designated ISACA as the exclusive credentialing authority for its Cybersecurity Maturity Model

As the digital landscape expands at an unprecedented rate, organizations are grappling with an increasingly complex and porous attack surface, making the proactive management of cyber threats more critical than ever before. In a significant move to address this challenge, cybersecurity firm

The breathtaking speed at which artificial intelligence is reshaping our world is matched only by the unsettling quiet surrounding its profound and systemic security flaws. As large language models (LLMs) become more powerful and integrated into our daily lives, a critical examination of their
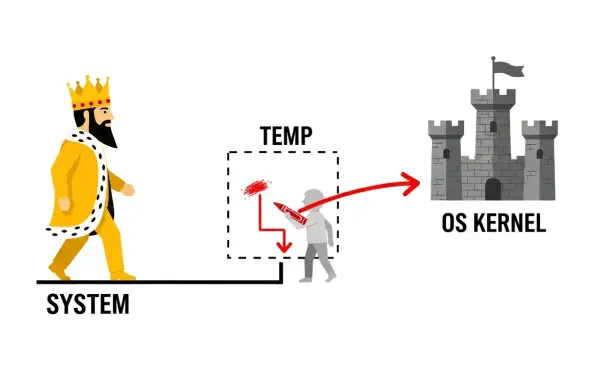
Introduction A seemingly harmless software uninstallation process can become the unlocked back door for an attacker, a reality recently underscored by a critical vulnerability discovered within the widely used JumpCloud platform. The platform, a cornerstone of IT management for thousands of
Our Picks
