
Jason Costain
Data Protection SpecialistJason Costain is a security expert specializing in personal data protection. He offers rich insights into incident response planning, cloud security best practices, and the importance of multifactor authentication. With his highly applicable and easy-to-understand publications, Jason empowers his readers with the best methods to protect their sensitive data.
Malik Haidar has spent years inside multinationals translating threat intelligence into boardroom-ready decisions, bridging analytics with business impact. In this conversation with Jason Costain, he unpacks what an early, Lua‑powered sabotage platform reveals about state priorities, how k

Malik Haidar stands at the intersection of high-stakes corporate defense and cutting-edge threat intelligence. With a career dedicated to dismantling the strategies of sophisticated hackers within multinational infrastructures, he has become a leading voice on how business logic must integrate with

The heavy rattle of a janitor’s keychain has become an obsolete soundtrack in a world where smartphones act as universal passports for every door and transaction. In a society that has largely moved toward contactless payments and mobile-first interactions, the clatter of mechanical locks and the f

The High-Stakes Debate Over American Surveillance Authority The legislative landscape surrounding the United States' surveillance capabilities recently underwent a period of intense volatility, culminating in a short-term extension of key spying powers that had previously been considered

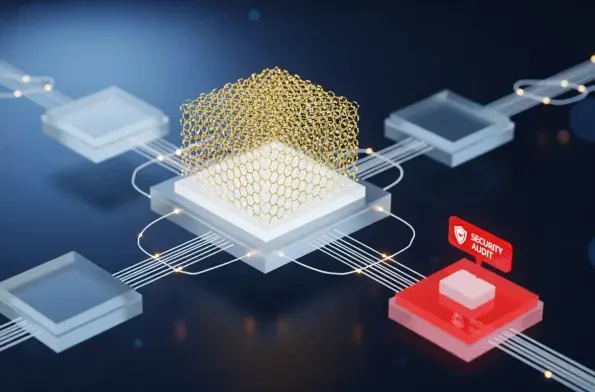
The modern software development lifecycle relies heavily on a complex web of interconnected cloud services, but a recent security breach at Vercel has demonstrated how a single weak link in this chain can expose entire organizational infrastructures to sophisticated threat actors. The incident
The deceptive simplicity of modern remote hiring processes has inadvertently created a massive gateway for international cyber-criminals seeking to exploit corporate trust and national security vulnerabilities through highly sophisticated identity theft operations. This reality became starkly

Malik Haidar has spent years in the trenches of corporate defense, specializing in the intersection of high-stakes intelligence and business continuity. He possesses a deep understanding of how digital sieges impact the healthcare sector, having analyzed the evolving tactics of ransomware

Our Picks
