Vulnerability Assessment
Let me introduce Malik Haidar, a cybersecurity expert with a wealth of experience in protecting multinational corporations from sophisticated threats and hackers. With a deep background in analytics, intelligence, and security, Malik has a unique ability to blend business perspectives with
In an era where digital battlegrounds are as critical as physical ones, the U.S. Department of Defense has made a bold and somewhat controversial decision to scale back mandatory cybersecurity training for military personnel, redirecting focus toward mission-critical operations. This policy shift,

We’re thrilled to sit down with Malik Haidar, a seasoned cybersecurity expert with years of experience protecting multinational corporations from digital threats and hackers. With a deep background in analytics, intelligence, and security, Malik has a unique perspective on blending business s
A Critical Flaw in Enterprise Update Management In the heart of enterprise IT environments, a silent threat has emerged, compromising the very system designed to keep networks secure. Windows Server Update Services (WSUS), a cornerstone for managing Microsoft updates across vast organizational
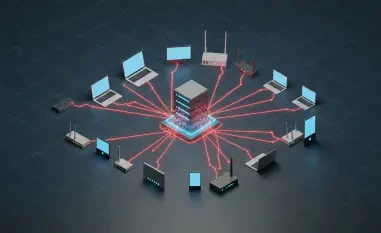
In an era where cyber espionage looms as a persistent threat to global security, a seemingly benign tool like ClickOnce, Microsoft's application deployment framework, has emerged as a potent weapon in the hands of sophisticated threat actors. Reports of targeted attacks on diplomatic entities

Meet Malik Haidar, a seasoned cybersecurity expert with a wealth of experience in safeguarding multinational corporations from digital threats and hackers. With a deep background in analytics, intelligence, and security, Malik has a unique ability to blend business perspectives with cutting-edge