Vulnerability Assessment
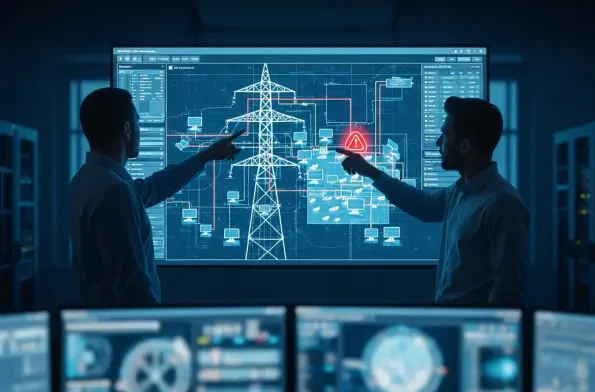
The very technology designed to secure Europe's energy future through clean, distributed power is quietly introducing a vulnerability that could bring the entire grid to a standstill. As solar panels blanket rooftops and fields in an unprecedented green transition, they are creating a vast,
A stark reminder of the persistent and evolving nature of cyber threats has emerged as the U.S. government’s top cybersecurity agency flagged four distinct, actively exploited vulnerabilities in some of the world's most common software. This research summary examines the U.S. Cybersecurity and

The relentless stream of daily security alerts has now officially become a firehose, with the annual number of Common Vulnerabilities and Exposures (CVEs) on track to surpass an unprecedented 50,000 this year alone. This staggering figure represents more than just a data point; it signals a
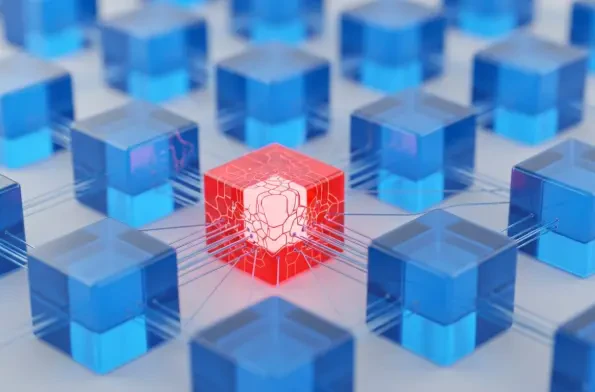
Introduction The silent digital gateways that manage vast corporate networks often harbor the most significant security risks, a reality recently underscored by a series of critical vulnerability disclosures from a major software provider. The release of a new security update for Ivanti's
The very trust that underpins the seamless functionality of our interconnected digital world has become the most fertile ground for a new generation of sophisticated cyber attacks. As organizations increasingly rely on a complex web of integrated tools, platforms, and automated systems, adversaries
In a stark reminder of the persistent threats facing digital ecosystems, Apple has issued emergency security updates across its product lines to neutralize a critical zero-day vulnerability that was already being exploited by attackers in the wild. The flaw, designated CVE-2026-20700, is a memory














