Threat Intelligence
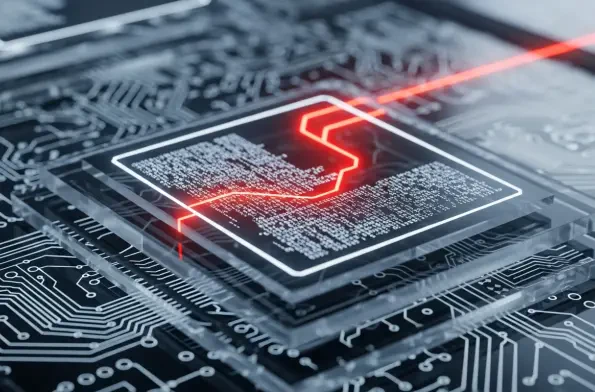
A startling discovery within a network of digital honeypots has provided definitive proof that threat actors are now successfully weaponizing Large Language Models to autonomously generate and deploy functional malware. Security researchers recently intercepted a malicious script that, while
The monthly ritual of software updates often feels like routine maintenance, but the latest security bulletin from Microsoft serves as a stark reminder of the persistent and evolving threats lurking in the digital landscape. February’s Patch Tuesday release addressed approximately 60 security f

The very foundation of digital trust that underpins modern business communication is crumbling under the weight of an unprecedented wave of sophisticated, AI-driven cyber attacks that existing defenses were never designed to handle. A staggering 88% of organizations have suffered a security

Microsoft has reported that a multi-stage intrusion campaign targeting internet-accessible SolarWinds Web Help Desk (WHD) instances for initial access may have exploited recently patched vulnerabilities before fixes were available. The sophisticated attacks, which took place in December 2025, saw

Amidst roiling domestic protests that capture global headlines, a parallel, quieter conflict wages on in the digital realm, one where Iran's state-sponsored cyber operatives show no signs of ceasing their espionage activities against a growing list of perceived adversaries. This persistent

The very fortress built to protect our most private conversations is now being turned against us, not with battering rams of code, but with whispers of deception that exploit the one vulnerability no encryption can patch: human trust. As high-value targets, from politicians and military leaders to