Threat Intelligence
The rapid convergence of sophisticated machine learning models and state-level offensive operations has fundamentally altered the digital battlefield by turning theoretical vulnerabilities into functional weapons. This transition marks a departure from the era where artificial intelligence was

The boundary between human ingenuity and machine-driven aggression has blurred to the point where a single modified line of code can now trigger a global security crisis without a person ever touching a keyboard. We have entered a period where the traditional "cat-and-mouse" game of
Analyzing the Weaponization of SaaS Platforms for Stealthy Cyber Surveillance In the quiet corridors of digital bureaucracy, a simple spreadsheet might appear as the ultimate symbol of corporate monotony, yet for state-sponsored actors, it has recently served as the perfect cloaking device for
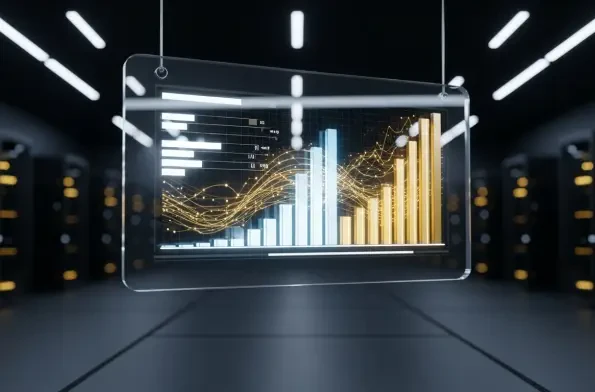
The emergence of a single, non-technical threat actor successfully compromising over 600 corporate networks across 55 countries in just a matter of weeks signals a definitive end to the era where sophisticated cyber warfare was the exclusive domain of nation-states. This shift is not driven by a
The extraction of high-level reasoning capabilities from frontier models represents a direct assault on the economic and safety foundations of the artificial intelligence industry. Recent security reports have illuminated a systemic pattern of "industrial-scale" distillation campaigns

The digital perimeter of the conflict in Ukraine has shifted from the localized energy grids of Kyiv to the highly secured servers of Western European financial institutions. While the world remains focused on the physical movement of troops, a more insidious campaign is unfolding within the














